- Testing, Inspection, & Certification
- Embedded Security Market
Embedded Security Market Size, Share, and Growth Forecast 2026–2033
Embedded Security Market by Component (Hardware, Software, Services), Application (Payment Security, Authentication & Identity Management, Secure Communication, Threat Detection & Intrusion Prevention, Others), Vertical (BFSI, IT & Telecom, Automotive, Healthcare, Consumer Electronics, Retail & E-commerce, Aerospace & Defence, Government & Public Sector, Others), and Regional Analysis, 2026–2033
Global Embedded Security Market Size and Trend Analysis
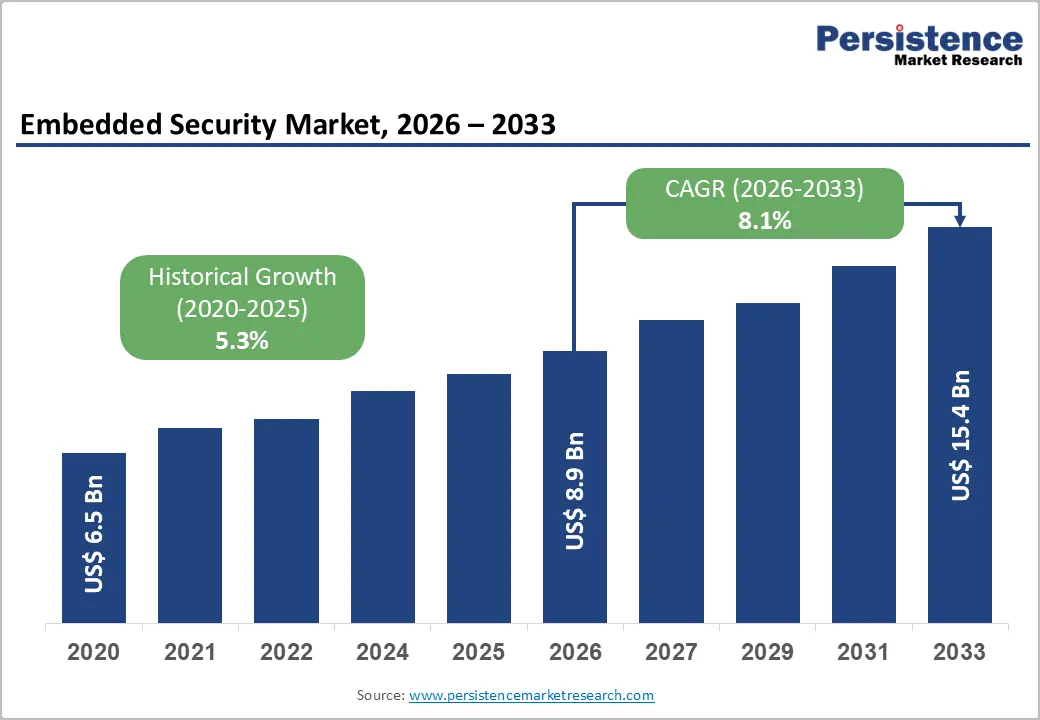
The global embedded security market is expected to be valued at US$ 8.9 billion in 2026 and is projected to reach US$ 15.4 billion by 2033, growing at a CAGR of 8.1% between 2026 and 2033, driven by the growing need to protect devices and systems from increasingly sophisticated cyber threats targeting hardware, firmware, and connected ecosystems. As industries adopt IoT, automotive electronics, and smart devices at scale, the risk of data breaches and system manipulation at the chip level has intensified.
Reliance on traditional software-based security has created strong demand for hardware-rooted trust, secure enclaves, and built-in cryptographic protection. Regulatory requirements such as the EU Cyber Resilience Act, NIST guidelines, and PCI DSS 4.0 are further reinforcing the need for embedded, compliance-ready security solutions across industries.
Key Industry Highlights:
- Leading Component: Hardware dominates the embedded security market with over 56.0% share in 2026, valued at more than US$ 5.0 billion, driven by the critical need for hardware-rooted trust anchors such as secure elements, TPMs, and HSMs in IoT, automotive, and critical infrastructure ecosystems.
- Leading Application: Payment security accounts for over 28.0% share in 2026, valued at more than US$ 2.49 billion, supported by widespread adoption of contactless payments, POS terminals, and smart card infrastructure under PCI DSS 4.0 and EMVCo compliance requirements.
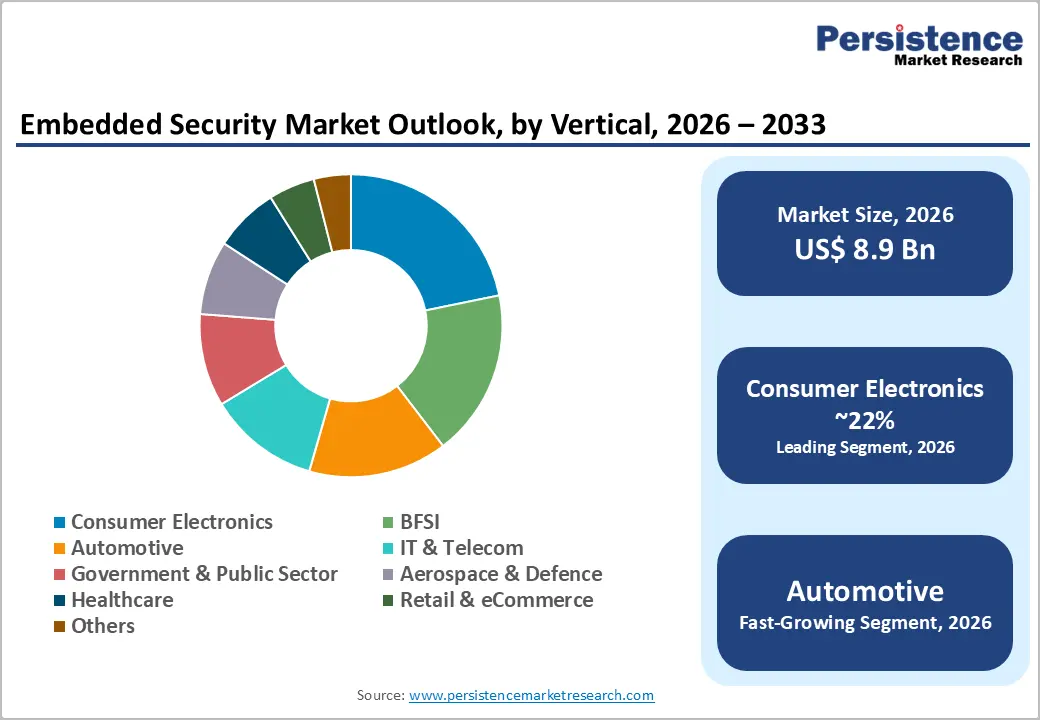
- Leading Vertical: Consumer Electronics holds over 22% share in 2026, valued at more than US$ 2.0 billion, driven by massive penetration of smartphones, wearables, smart home devices, and increasing reliance on secure boot and Trusted Execution Environments.
- Fastest Growing Vertical: Automotive is the fastest-growing vertical, driven by UNECE WP.29 compliance, software-defined vehicles, V2X communication, and expanding in-vehicle attack surfaces.
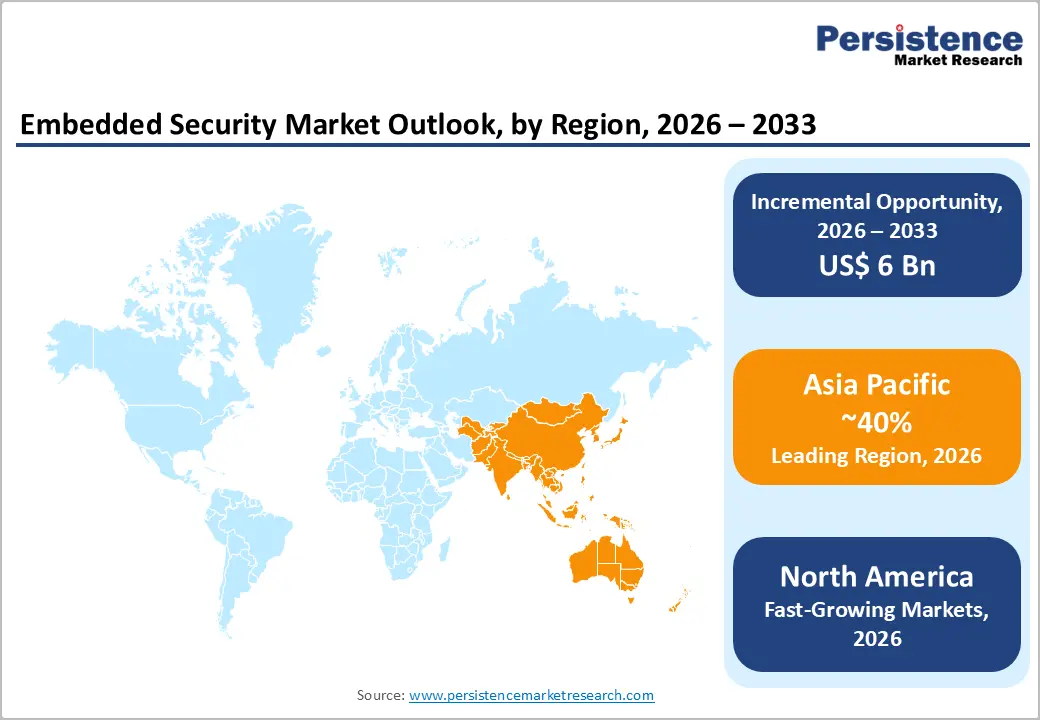
- Leading Region: Asia Pacific dominates with over 40% share in 2026, valued at US$ 3.6 billion, supported by large-scale electronics manufacturing, semiconductor ecosystems, and government-led digital infrastructure programs. It is also the fastest-growing region, driven by automotive electrification, IoT expansion, and national security standards in China, India, Japan, and South Korea.
Market Dynamics
Drivers - Explosive Growth of IoT Device Proliferation Mandating Hardware-Level Security
The rapid proliferation of internet-connected endpoints across industrial, consumer, and critical infrastructure environments is driving demand for the embedded security market. As device counts scale into the tens of billions globally, perimeter-based security models become structurally inadequate, forcing security to migrate into the device itself at the silicon or firmware layer.
Secure elements, Trusted Platform Modules (TPMs), and hardware security modules (HSMs) are now engineering requirements rather than optional add-ons for connected device certifications. Studies indicate that more than 70% of newly designed IoT platforms launched after 2023 incorporate some form of hardware root of trust, a figure that reflects how foundational embedded security has become to product architecture decisions.
Mounting Regulatory and Compliance Obligations Across Critical Sectors
The regulatory enforcement is creating mandatory baseline security requirements for connected devices. The EU Cyber Resilience Act, effective from 2024 with compliance deadlines extending to 2027, requires hardware and software manufacturers to embed security by design, directly expanding the addressable market for certified secure microcontrollers and security ICs. In the automotive sector, ISO/SAE 21434 and UNECE WP.29 Regulation No. 155 have made embedded cybersecurity compliance a condition of vehicle type approval across more than 54 countries. These regulatory frameworks function as demand-side shock absorbers, insulating embedded security market growth rate trajectories from broader macroeconomic softness.
Restraints - High Integration Complexity and Design-In Costs for Constrained Devices
Microcontrollers and edge processors used in low-power sensors, medical wearables, and industrial nodes operate under strict power, memory, and computational budgets that make standard security module integration technically challenging. This creates a design-in bottleneck where security requirements conflict with bill-of-materials constraints, particularly for original equipment manufacturers (OEMs) competing in cost-sensitive segments. The consequence is delayed security integration timelines, leaving a meaningful proportion of deployed devices operating below current regulatory standards and creating liability exposure for manufacturers and platform operators alike.
Fragmented Standards Ecosystem Creating Interoperability Barriers
The embedded security industry operates across a fractured standards landscape, where competing certification frameworks, such as Common Criteria, FIDO Alliance, GlobalPlatform, PSA Certified, and sector-specific regimes impose overlapping and sometimes contradictory requirements on device makers. This fragmentation elevates compliance costs and extends time-to-market, especially for manufacturers targeting multi-regional distribution. A device certified under one jurisdiction's requirements requires full re-evaluation for another market, disproportionately burdening smaller vendors and creating market consolidation pressure that slows innovation at the mid-tier. The absence of a globally harmonised embedded security certification standard remains one of the most actionable policy gaps in the sector.
Opportunities - Post-Quantum Cryptography Transition as a Generational Replacement Cycle
The imminent transition to post-quantum cryptography (PQC) standards represents the most consequential hardware replacement cycles the embedded security industry has encountered in a generation. The U.S. National Institute of Standards and Technology (NIST) finalised its first set of PQC algorithms in 2024, triggering mandatory migration timelines across federal procurement and cascading into commercial sectors.
Silicon vendors and HSM manufacturers should treat PQC as a strategic product roadmap priority, developing hardware-accelerated implementations of CRYSTALS-Kyber and CRYSTALS-Dilithium algorithms before competitors commoditise the transition. Government procurement agencies, financial institutions, and critical infrastructure operators represent the highest-value early-adopter cohort, and vendors who achieve PQC certification will secure long-term design wins that carry multi-year revenue visibility.
Automotive Embedded Security as a High-Growth Vertical Driven by Vehicle Electrification and Connectivity
Modern vehicles incorporate more than 100 electronic control units (ECUs), each representing a potential attack surface, alongside over-the-air (OTA) update capabilities, vehicle-to-everything (V2X) communication interfaces, and centralised domain controllers that require cryptographic key management at scale. The average hardware security content per vehicle is projected to increase by more than 60% as automakers transition to software-defined vehicle architectures. Vendors who invest in automotive-grade secure element certification under AEC-Q100 and align product roadmaps with ISO/SAE 21434 requirements position themselves for embedded security market revenue outlook advantages as global vehicle production volumes recover and electrification rates accelerate through 2033.
Category-wise Analysis
Component Insights
Hardware accounts for more than 56.0% of the global Embedded Security market in 2026, equivalent to US$ 5.0 billion, driven by the critical need for immutable trust anchors in increasingly connected and attack-prone digital ecosystems. As cyber threats shift toward firmware, IoT endpoints, and edge devices, enterprises require tamper-resistant hardware such as secure microcontrollers, TPMs, HSMs, and embedded Secure Elements (eSEs) to establish a reliable hardware root of trust that software alone cannot ensure. This need is further reinforced by regulatory and certification frameworks such as Common Criteria (EAL5+) and PSA Certified, which mandate or strongly encourage hardware-based implementations for high-assurance environments, structurally sustaining long-term demand for hardware-centric embedded security solutions.
Software is emerging as the fastest-growing component category, due to the increasing need to secure highly connected and continuously updated device ecosystems. As organizations deploy large-scale IoT, automotive, and industrial systems, there is a growing requirement for security layers that extend beyond hardware roots of trust to include Trusted Execution Environment (TEE) management, secure firmware-over-the-air (FOTA) updates, and lifecycle-based vulnerability protection. This shift is being fueled by the need for real-time threat mitigation, remote patching capabilities, and compliance with evolving cybersecurity regulations across connected environments.
Application Insights
The payment security segment accounts for over 28.0% share of the global Embedded Security market in 2026, reaching over US$ 2.49 billion value, supported by widespread deployment of contactless payment infrastructure across POS terminals, smart cards, mobile wallets, and wearable devices. The growth is primarily driven by stringent compliance requirements under PCI DSS 4.0 and EMVCo standards, which mandate secure element integration and robust cryptographic protection at the device level. This creates structurally recurring demand linked to payment volume growth, device refresh cycles, and continuous regulatory tightening.
Authentication & identity management is the fast-growing application, due to the global expansion of digital identity programmes, biometric passport issuance, and enterprise adoption of zero-trust architectures. These developments are increasing demand for hardware-backed credential storage to meet higher assurance requirements under modern identity security frameworks. Vendors operating across both payment and identity ecosystems are well-positioned to benefit from convergence trends, as secure element platforms increasingly support multiple use cases such as payments, identity verification, and access control within a single embedded security chip.
Vertical Insights
Consumer electronics account for over 22.0% share in 2026, surpassing US$ 2.0 billion value, driven by the massive installed base of smartphones, smart home devices, wearables, and connected audio-visual systems. This segment leads embedded security adoption due to escalating requirements for device authentication, data protection, and hardware-level trust enforcement, including secure boot mechanisms, Trusted Execution Environments (TEE), and secure elements. The expansion of IoT connectivity has significantly increased the attack surface, making embedded, hardware-rooted security essential rather than optional in consumer ecosystems.
Automotive is emerging as the fastest-growing vertical, due to mandatory cybersecurity compliance requirements under UNECE WP.29, the rapid shift toward software-defined vehicles, and the increasing integration of connected systems such as telematics, ADAS, and V2X communication. These advancements significantly expand the vehicle’s digital attack surface, creating a strong need for embedded cryptographic protection, secure boot mechanisms, and hardware-rooted trust to ensure system integrity and safety across the vehicle lifecycle.
Regional Insights
North America Embedded Security Market Trends and Insights
North America accounts for more than 26% of the global Embedded Security market in 2026, representing US$ 2.3 billion. The region's demand structure is anchored by the concentration of hyperscale cloud infrastructure, advanced semiconductor design capability, and the world's most mature regulatory enforcement environment for cybersecurity, including CISA mandates, NIST framework adoption, and FedRAMP requirements. North America's market growth will increasingly be shaped by the PQC migration cycle and the expansion of domestic semiconductor manufacturing under the CHIPS and Science Act, which incentivises onshore secure silicon production.
The United States Embedded Security market accounts for over 83.0% of the North America regional market in 2026, reaching over to US$ 1.9 Billion value, driven by federal cybersecurity mandates, the defence-industrial complex's requirements for tamper-evident hardware modules, and the concentration of leading semiconductor design houses that both consume and supply embedded security components. The U.S. market is further reinforced by the Cybersecurity Executive Order 14028, which mandates software supply chain security standards that extend to firmware and embedded systems.
Europe Embedded Security Market Trends and Insights
Europe is expected to account for over 20.0% of the global Embedded Security market in 2026, representing US$ 1.8 billion, and operates under the most prescriptive regulatory environment for embedded device security in the world. The EU Cyber Resilience Act, NIS2 Directive, and GDPR collectively mandate security-by-design principles across connected products, industrial systems, and critical infrastructure, creating structurally elevated compliance-driven demand. Germany Embedded Security market represents more than 23.0% of the Europe regional market in 2026, surpassing over US$ 410 million. Germany's Federal Office for Information Security (BSI) actively shapes national embedded security standards and certification requirements, creating a home-market compliance environment that rewards domestically certified vendors.
The United Kingdom Embedded Security market accounts US$ 320 million value in 2026, driven by a combination of financial services sector demand, defence procurement, and the country's proactive Product Security and Telecommunications Infrastructure (PSTI) Act enforcement. The UK's position as a global fintech hub creates sustained demand for payment security hardware and authentication-embedded security solutions, with City of London financial institutions among the most aggressive adopters of hardware-backed key management infrastructure.
Asia Pacific Embedded Security Market Trends and Insights
Asia Pacific accounts for over 40.0% of the global Embedded Security market in 2026, representing US$ 3.6 billion, making it the dominant regional market and the fastest growing region globally at a projected CAGR of 12.8% through 2033. The region's structural acceleration reflects an extraordinary concentration of semiconductor manufacturing, electronics OEM production, and large-scale government-led digital identity and smart city programmes. China Embedded Security market represents 42.0% of the Asia Pacific regional market in 2026, equivalent to US$ 1.5 billion, driven by the world's largest consumer electronics and electric vehicle manufacturing base, combined with government-mandated security standards for connected devices. China's GB/T embedded security standards and the Multi-Level Protection Scheme (MLPS 2.0) create mandatory compliance demand.
Japan Embedded Security market is expected to exceed US$ 570 million in 2026, due to the country's advanced automotive electronics sector and a mature industrial IoT manufacturing base. Japan's semiconductor resurgence, anchored by the Rapidus initiative and TSMC's Kumamoto fab, will strengthen domestic embedded security component supply chains and technology capability. The South Korea Embedded Security market is expected to reach over US$ 430 billion by 2026, supported by the country's world-class semiconductor industry and its dominant position in memory chip and display panel manufacturing.
India Embedded Security market is the fastest-growing country. India's Digital Public Infrastructure stack, including Aadhaar biometric identity, UPI payment rails, and DigiYatra creates sustained demand for embedded authentication and payment security hardware across billions of registered users and millions of access points. The government's Semiconductor Mission and PLI scheme for electronics manufacturing are actively building domestic embedded security chip production capacity, reducing import dependency.
Competitive Landscape
The global embedded security market is a moderately consolidated structure where the top companies collectively account for a majority of the hardware segment revenue. Strategic competition centres on silicon-level differentiation through proprietary secure element architectures and EAL certification depth; software and platform integration capability that extends hardware revenue with high-margin security lifecycle services; and standards leadership through active participation in GlobalPlatform, FIDO Alliance, PSA Certified, and ETSI working groups. The most consequential strategic shift underway is the transition from transactional component selling toward recurring managed security service models, where embedded hardware becomes the anchor for subscription-based key management, remote attestation, and device lifecycle orchestration revenues.
Key Developments:
- In March 2026, Exein launched a next-generation runtime security solution designed to protect AI-native and IoT devices by operating directly at the kernel level. Technology enables real-time threat detection and prevention within embedded systems, addressing growing security risks in connected and AI-driven environments.
- In January 2026, MITRE launched the Embedded Systems Threat Matrix (ESTM), a cybersecurity framework designed to identify and mitigate threats across hardware, firmware, and cyber-physical systems. The initiative aims to strengthen security in critical sectors like healthcare, industrial control, and transportation, while creating a standardized approach to embedded system threat analysis and defense.
Companies Covered in Embedded Security Market
- Infineon Technologies
- NXP Semiconductors
- STMicroelectronics
- Microchip Technology
- Renesas Electronics
- Texas Instruments
- Samsung Electronics
- Broadcom
- Qualcomm
- Nuvoton Technology
- Thales Group
- IBM
- Entrust
- Arm Holdings
- Others
Frequently Asked Questions
The embedded security market is valued at US$ 8.9 billion in 2026 and is projected to reach US$ 15.4 Billion by 2033, driven by the rising need to secure IoT devices and ensure hardware-rooted trust in connected ecosystems.
The growth is driven by the surge in connected IoT deployments and mandatory cybersecurity compliance requirements across industries. Regulations such as the EU Cyber Resilience Act and UNECE WP.29 are making embedded security a non-negotiable requirement for manufacturers.
Hardware segment leads the market with 56% share in 2026 due to the need for certified, tamper-resistant security foundations. Industries prefer hardware-based security as software-only solutions cannot meet regulatory-grade protection requirements.
Asia Pacific dominates with over 40% share in 2026, driven by large-scale electronics and EV manufacturing and strong government-led digital identity programs. High adoption of secure hardware in China, India, and South Korea further strengthens regional demand.
The key opportunity lies in the shift toward post-quantum cryptography hardware upgrades driven by new NIST standards. This is creating a replacement cycle for secure elements and HSMs across government, automotive, and financial sectors, making early adoption critical for vendors.
The leading companies in the Embedded Security market include Infineon Technologies, NXP Semiconductors, STMicroelectronics, Microchip Technology, Renesas Electronics, Texas Instruments, and Samsung Electronics, among others.








