- Automotive Components & Materials
- Automotive Cybersecurity Market
Automotive Cybersecurity Market Size, Share, and Growth Forecast for 2026 - 2033
Automotive Cybersecurity Market by Component [Hardware (Hardware Security Modules (HSMs), Secure Vehicle Network Gateways, Trusted Platform Modules (TPM), and Others), Software (Embedded Firewalls Encryption & Cryptography, Biometrics & Authentication Others), Vehicle (Autonomous Vehicles Semi-autonomous Vehicle Non-autonomous Vehicle), Services), Application, Vehicle, and Regional Analysis for 2026 - 2033
Automotive Cybersecurity Market Size and Trends Analysis
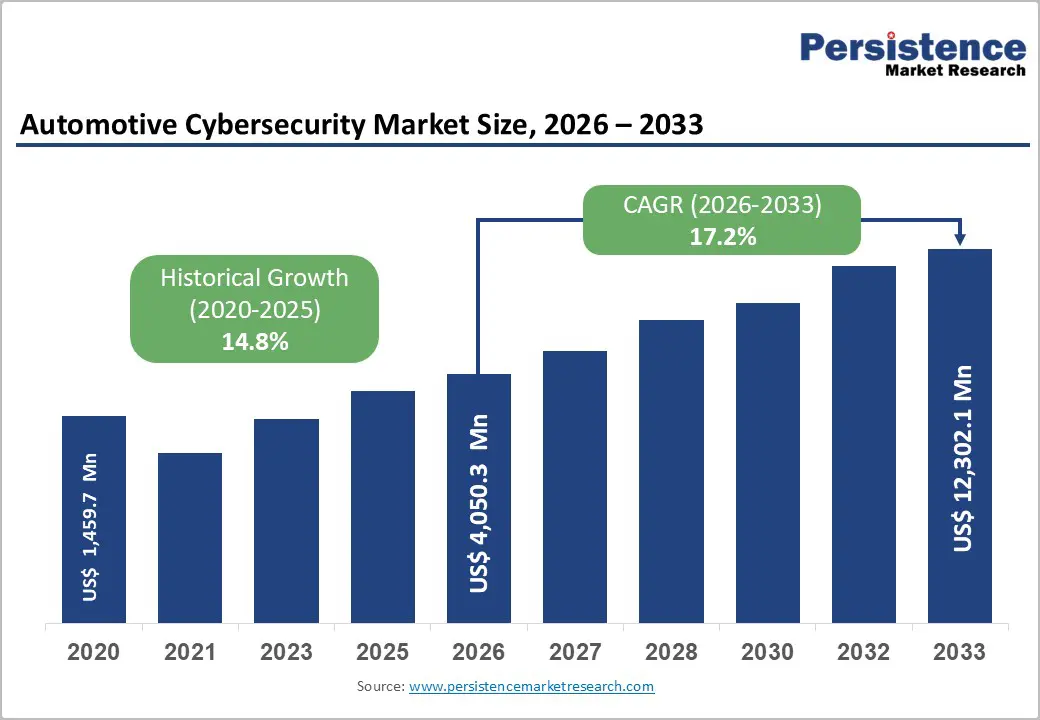
The global automotive cybersecurity market is projected to expand nearly threefold, rising from US$ 4,050.3 million in 2026 to US$ 12,302.1 million by 2033, registering a robust CAGR of 17.2%.
The market growth is primarily driven by tightening government cybersecurity regulations and rapid advancements in connected vehicle technologies. As automakers integrate advanced safety and connectivity features such as automatic emergency braking, lane departure warning systems, and vehicle-to-everything (V2X) communication, the risk of cyber threats increases. This is accelerating investments in secure software architectures, over-the-air (OTA) updates, and end-to-end vehicle cybersecurity solutions across global automotive ecosystems.
Key Industry Highlights:
- Hardware cybersecurity solutions dominate with a 59.4% market share in 2026, mainly driven by Hardware Security Modules (HSMs) embedded in ECUs.
- ADAS & Safety Systems form the largest application segment due to critical safety features vulnerable to cyberattacks, holding over 30% market share.
- Complex automotive supply chains and inconsistent cybersecurity standards across tiers create vulnerabilities and hinder effective end-to-end security enforcement.
- The transition to Software-Defined Vehicles (SDVs) offers cybersecurity vendors new opportunities through lifecycle security and secure over-the-air (OTA) software management.
- Digital transformation in EV manufacturing introduces new attack surfaces, driving demand for cybersecurity across operational and information technology layers.
- Adoption of Zero Trust Architecture (ZTA) is increasing, ensuring strict access controls and continuous verification in connected and autonomous vehicle ecosystems.
- Strategic acquisitions, like Option 3’s purchase of Onclave Networks, strengthen Zero Trust cybersecurity solutions tailored to automotive industry needs.
- BlackBerry’s QNX OS for Safety now includes a certified integrity-checking filesystem, enhancing runtime safety-critical system validation per ISO 26262 standards.
- Supply chain vulnerabilities remain a major restraint, as lower-tier suppliers may lack compliance, complicating real-time threat response and security management.
| Key Insights | Details |
|---|---|
|
Automotive Cybersecurity Market Size (2026E) |
US$ 4,050.3 Mn |
|
Market Value Forecast (2033F) |
US$ 12,302.1 Mn |
|
Projected Growth (CAGR 2026 to 2033) |
17.2% |
|
Historical Market Growth (CAGR 2020 to 2025) |
14.8% |
Market Dynamics
Drivers - Regulatory Mandates like UNECE WP.29 and ISO/SAE 21434 Surge the demand for Automotive Cybersecurity
International automotive cybersecurity regulations are a primary growth catalyst for the global market. The UNECE WP.29 framework mandates Regulations R155 and R156, requiring Cybersecurity Management Systems (CSMS) and Software Update Management Systems (SUMS) for vehicle type approval across the European Union, with growing influence in Asia-Pacific and other regions. These rules compel automakers to implement structured risk assessments, vulnerability monitoring, incident response protocols, and secure over-the-air (OTA) software update mechanisms.
Supporting this framework, ISO/SAE 21434 establishes engineering-level cybersecurity requirements throughout the vehicle lifecycle, from design and development to post-production operations. Leading OEMs such as BMW, Mercedes-Benz, and Toyota are significantly increasing investments to ensure compliance, as regulatory failure can restrict access to key global markets.
In 2024, BlackBerry confirmed that its QNX operating system meets ISO 21434 and ISO 26262 standards, reflecting industry-wide adaptation. As connected and autonomous vehicles expand, regulatory compliance will remain central to ensuring safety, strengthening consumer trust, and accelerating demand for advanced automotive cybersecurity solutions worldwide.
Restraint - Supply Chain Complexity and Vulnerability Hampers the Market Growth
The global automotive supply chain is highly complex and interconnected, involving OEMs, Tier-1 and Tier-2 suppliers, software developers, semiconductor manufacturers, cloud providers, and logistics partners across multiple regions. While this ecosystem drives innovation and operational efficiency, it significantly expands the cybersecurity attack surface. Each supplier or technology partner introduces potential vulnerabilities, making it challenging for automakers to maintain a unified, end-to-end cybersecurity framework.
In 2024, a cyberattack on a Tier-1 automotive software supplier disrupted several vehicle platforms worldwide, causing production delays and exposing sensitive customer and vehicle data. Major OEMs such as Stellantis and Hyundai Motor Company were indirectly affected, highlighting systemic risks linked to third-party dependencies.
The issue is compounded by uneven compliance with regulations like UNECE R155. While leading OEMs implement structured Cybersecurity Management Systems (CSMS), many lower-tier suppliers lack technical maturity and resources. Additionally, continuous audits, real-time monitoring, and cross-border compliance management increase operational costs.
Without standardized security frameworks, shared threat intelligence, and integrated supply chain risk management platforms, supply chain fragmentation will remain a critical restraint on the global automotive cybersecurity market’s long-term growth.
Opportunity - Rise of Software-Defined Vehicles (SDVs)
The automotive industry is rapidly evolving toward Software-Defined Vehicles (SDVs), where core functionalities are increasingly controlled by software rather than hardware components. This shift is fundamentally transforming vehicle architecture and expanding the demand for embedded automotive cybersecurity solutions. As vehicles become highly connected digital platforms, cybersecurity must be integrated from the design stage to ensure functional safety and regulatory compliance.
In 2024, BlackBerry introduced the QNX® Filesystem for Safety (QFS), a POSIX-compliant, ISO 26262 ASIL B-certified solution that validates real-time data integrity critical in SDVs where corrupted files could compromise braking, steering, or ADAS functions. SDVs depend on constant connectivity for over-the-air (OTA) updates, diagnostics, and feature enhancements.
OEMs such as Mercedes-Benz and General Motors have established dedicated software divisions to manage secure software ecosystems in line with UNECE R156 requirements. As vehicles become “computers on wheels,” demand is accelerating for intrusion detection systems, secure boot technologies, and lifecycle-focused cybersecurity platforms that ensure safety and data privacy.
Digital Transformation in EV and Smart Manufacturing
The accelerating adoption of electric vehicles (EVs) is driving manufacturers to digitize production processes and implement Industry 4.0-based smart manufacturing systems. This transformation is expanding cybersecurity requirements across both Operational Technology (OT) and Information Technology (IT) infrastructures. EV production relies heavily on connected robotics, cloud-based analytics, battery management systems, and automated supply chain networks, significantly increasing cyber risk exposure.
Industrial leaders such as Rockwell Automation are delivering comprehensive cybersecurity solutions, including vulnerability assessments, network segmentation, firewall-protected micro-perimeters, and secure remote access frameworks. In 2024, a global EV manufacturer implementing Rockwell’s Connected Enterprise® approach reported a 70% reduction in safety downtime due to improved data integration and real-time threat monitoring. As IT and OT environments converge, cybersecurity providers are expanding 24/7 threat detection, incident response, and managed security services tailored for smart factories. This digital shift positions industrial cybersecurity as a critical enabler of secure EV production and long-term operational resilience.
Automotive Cybersecurity Market Insights and Trends
Manufacturers are Adopting Zero Trust Cybersecurity Architectures
Zero Trust architecture (ZTA) is gaining momentum as the automotive industry recognizes the limitations of traditional perimeter-based security. ZTA assumes no user, device, or system should be trusted by default, regardless of location an essential philosophy for modern connected and autonomous vehicles.
- In August 2024, Option 3's acquisition of Onclave Networks showcased this shift. Onclave’s cybersecurity solutions, inspired by U.S. Department of Defense frameworks, introduced strict access controls, microsegmentation, and identity-based authentication. These measures help reduce attack surfaces, mitigate lateral movement in networks, and simplify security monitoring.
The increasing number of ransomware attacks on automotive IT systems including suppliers and retailers has prompted OEMs to adopt ZTA in both manufacturing and vehicle platforms. With telematics systems, cloud-connected infotainment, and V2X communications being vulnerable, ZTA ensures that every component is continuously verified before granting access.
OEMs like Ford and Stellantis are experimenting with Zero Trust within their smart manufacturing environments to secure critical infrastructure. ZTA is expected to become the default cybersecurity architecture in automotive development over the next few years, influencing product design, supplier onboarding, and customer data privacy protocols.
Category-wise Analysis
Component Insights
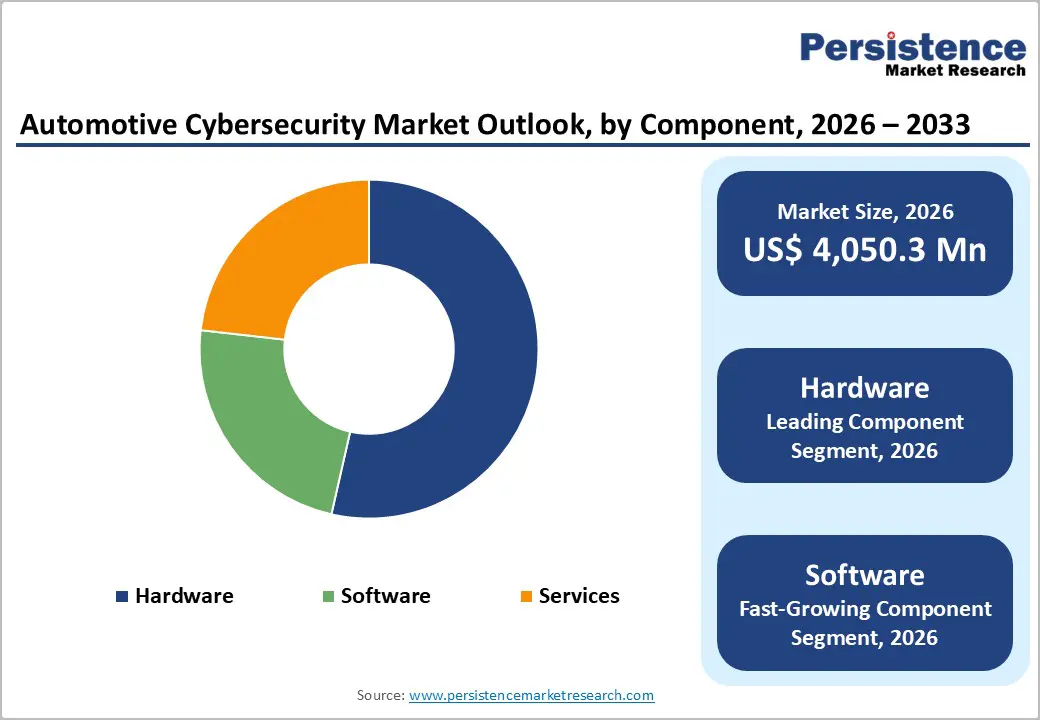
The hardware segment of the Global Automotive Cybersecurity Market is expected to retain its leadership in 2026, accounting for approximately 59.4% of total revenue, underscoring its critical role in building secure vehicle architecture. As vehicles transition toward connected, electric, and software-defined platforms, hardware-based security remains fundamental to protecting electronic control units (ECUs), in-vehicle networks, and external communication interfaces. According to industry analysis, the segment is projected to grow at a strong CAGR of 16.9% during the forecast period, reflecting sustained OEM investment in embedded security systems.
Key components include Hardware Security Modules (HSMs), Secure Vehicle Network Gateways, and Trusted Platform Modules (TPMs). Among these, HSMs are the most widely adopted due to their advanced cryptographic capabilities. Integrated directly into ECUs, HSMs enable secure key storage, encryption and decryption, digital signature authentication, and secure boot processes ensuring protection against unauthorized access, cyberattacks, and data manipulation.
However, hardware-based solutions can increase integration complexity and production costs, particularly in vehicles with multiple interconnected ECUs. As over-the-air (OTA) updates and cloud connectivity expand, OEMs are increasingly adopting hybrid and software-defined security models to complement hardware protection and address evolving cyber threats.
Application Insights
The automotive cybersecurity market, segmented by application into telematics, infotainment systems, powertrain systems, ADAS & safety systems, body control systems, and others are witnessing strong momentum in advanced safety technologies. Among these, ADAS & safety systems are expected to dominate, accounting for over 30% share in 2026.
ADAS cybersecurity leads due to its direct impact on vehicle control and passenger safety. Core functions such as Adaptive Cruise Control, Lane Keep Assist, and Automatic Emergency Braking rely on interconnected sensors, radar, LiDAR, cameras, and embedded software, creating a broad cyberattack surface. Securing internal communication protocols like CAN, LIN, and automotive Ethernet, along with external V2X connectivity, is critical to preventing spoofing, signal manipulation, and remote intrusion attacks.
Automakers are increasingly deploying intrusion detection systems, encrypted communication layers, secure coding practices, and protected over-the-air (OTA) updates to safeguard ADAS platforms. Because these systems directly control braking, steering, and acceleration, any security breach poses severe safety and liability risks. As vehicles move toward higher automation levels, cybersecurity integration within ADAS remains a strategic priority for regulatory compliance, system integrity, and consumer trust.
Vehicle Anatomy Insights
In the global automotive cybersecurity market, semi-autonomous vehicles represent the dominating segment, accounting for approximately 52–58% of total market revenue in 2026. This dominance is primarily driven by the widespread integration of Advanced Driver Assistance Systems (ADAS) such as adaptive cruise control, lane-keeping assist, automated emergency braking, and connected infotainment platforms.
According to global vehicle production trends, over 60% of newly produced passenger vehicles now incorporate Level 1–Level 2 automation features, significantly increasing the cybersecurity attack surface across ECUs, CAN networks, telematics control units, and OTA software systems. Regulatory mandates such as UNECE WP.29 cybersecurity compliance further accelerate cybersecurity adoption in semi-autonomous platforms, reinforcing their revenue leadership.
Autonomous Vehicles (Level 4–Level 5) are projected to be the fastest-growing segment, registering an estimated CAGR of 18–22% during 2026–2033. Although current deployment volumes remain limited, cybersecurity spending per vehicle is substantially higher due to AI-driven systems, LiDAR, radar, V2X communication, and cloud-based data exchange requirements. In contrast, the non-autonomous vehicles hold a smaller and gradually declining share, as minimal connectivity reduces cybersecurity investment intensity compared to connected and semi-autonomous vehicle platforms.
Regional Insights and Trends
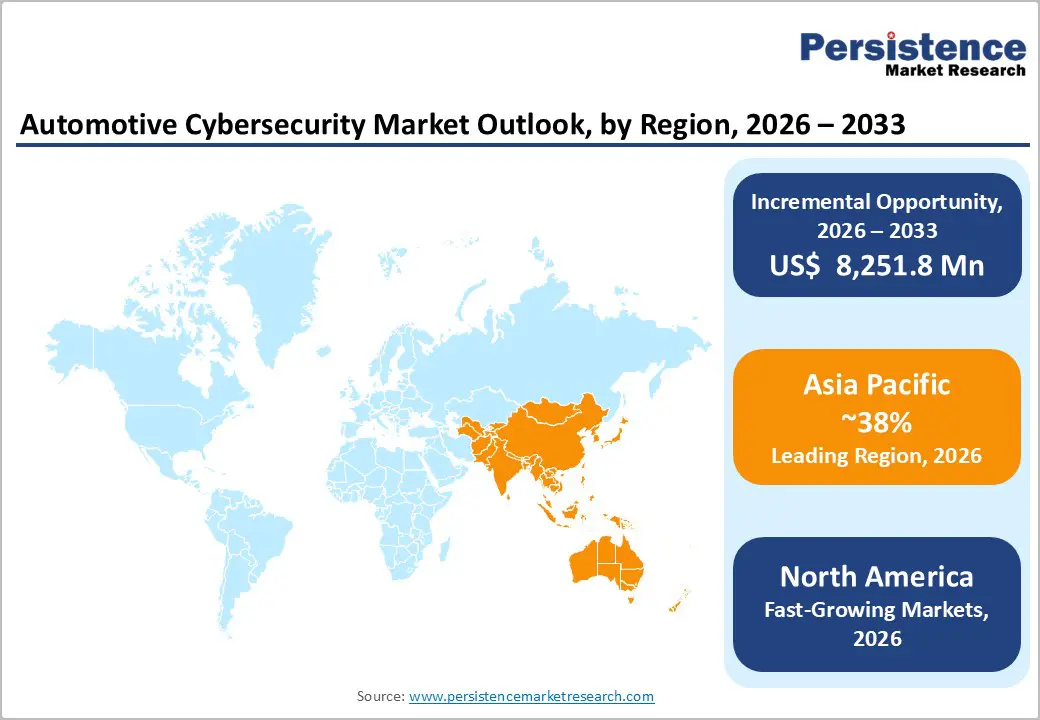
Asia Pacific Autonomous Cybersecurity Market
Asia Pacific is set to dominate the global automotive cybersecurity market, driven by large-scale connected vehicle production and accelerating digital transformation. According to Persistence Market Research, the region is projected to hold 37.4% share in 2026 and expand at a robust 17.1% CAGR through 2033. Growth is fueled by strong automotive ecosystems in China, India, Japan, and South Korea, alongside rising electric vehicle (EV) adoption and software-defined vehicle integration.
China leads the regional landscape with aggressive regulatory development. In 2024, it introduced the GB 44495-2024 cybersecurity standard for intelligent vehicles, aligned with global frameworks while tailored to domestic priorities. With nearly 100 automotive cybersecurity-related regulations expected by 2025, China is strengthening OTA security, data protection, and vehicle network safeguards. Its dominance in EV manufacturing further reinforces its global influence despite geopolitical constraints.
India is rapidly advancing cybersecurity compliance, aligning with ISO/SAE 21434 and UNECE WP.29 standards. Government initiatives such as Digital India, combined with expanding telematics adoption, are driving demand for robust data and infrastructure protection.
Japan, leveraging advanced automotive engineering and adherence to UNECE R155 standards, prioritizes lifecycle cybersecurity, supply chain risk management, and incident response frameworks ensuring sustained competitiveness in the connected mobility era.
North America ranks second in the Demand for Automotive Cybersecurity
The North America Automotive Cybersecurity Market holds a 27.1% global market share and is projected to expand at a 17.4% CAGR from 2026 to 2033, driven by strict regulatory mandates, rapid adoption of connected vehicles and EVs, and escalating cyber threats. In the U.S., the National Highway Traffic Safety Administration issued updated cybersecurity guidelines in 2023, while the Department of Commerce proposed restrictions in 2024 on certain foreign technologies in connected vehicles, reinforcing national security priorities. Canada is aligning with ISO/SAE 21434 and developing its own cybersecurity framework for connected and autonomous vehicles.
Technology innovation remains central to growth. Companies such as Argus Cyber Security deploy AI-based threat detection systems, while NXP Semiconductors provides secure automotive microcontrollers. Automakers, including Ford Motor Company and General Motors, are integrating Trusted Platform Modules (TPMs), and Tesla continues to lead in secure over-the-air (OTA) updates.
Strategic partnerships and investments, alongside rising cyber incidents over 50 reported attacks in 2024, are accelerating the adoption of vehicle Security Operations Centers (vSOCs), V2X protection systems, and cloud-based cybersecurity platforms, strengthening North America’s leadership in automotive digital security.
Competitive Landscape
The automotive cybersecurity market features a dynamic competitive landscape driven by collaborations, innovations, and strategic acquisitions. Key players are joining forces to advance cybersecurity technologies and meet industry-specific and regional demands. ETAS Korea partnered with Suresoft Tech to enhance in-vehicle cybersecurity testing, while NXP Semiconductors collaborated with Moter Technologies to combine automotive chipsets with machine learning software.
BlackBerry upgraded its QNX OS for Safety with a certified integrity-checking filesystem, boosting runtime validation for safety-critical systems. Additionally, Option 3’s cybersecurity platform ENIGMA acquired Onclave Networks, integrating advanced Zero Trust architecture modeled after U.S. defense standards. These initiatives highlight the industry's focus on robust, scalable, and compliant cybersecurity solutions.
Key Industry Developments:
- In 2026, At CES 2026, Autocrypt introduced Automotive-CIS, a lifecycle-based cybersecurity infrastructure standard. This framework integrates CSMS, SUMS, vSOC, and TARA into a unified architecture, addressing security from development through maintenance. The move reflects a structural market shift toward integrated, end-to-end cybersecurity solutions as the industry transitions to software-defined and AI-driven vehicles.
- In September 2024, BlackBerry Limited advanced its QNX® OS for Safety by integrating a POSIX-compliant, ISO 26262-certified integrity-checking filesystem. This enhancement introduces an additional layer of validation for safety-critical systems, benefiting OEMs and embedded software providers. The newly introduced QNX® Filesystem for Safety (QFS), certified to ISO 26262 ASIL B, actively verifies filesystem integrity during runtime, allowing developers to detect and mitigate corruption to uphold system safety.
- In August 2024, Option 3 revealed that its cybersecurity platform, ENIGMA, had acquired Onclave Networks. ENIGMA emphasizes Zero Trust architecture, a rapidly emerging cybersecurity model as traditional approaches face diminishing returns. Onclave brings with it a robust implementation of Zero Trust principles, inspired by methodologies from the U.S. Department of Defense. These practices substantially minimize security breaches, reduce attack surfaces and network complexity, and lower operational costs. The acquisition strengthens ENIGMA's ability to safeguard devices, services, and personnel across varied operational environments.
Companies Covered in Automotive Cybersecurity Market
- Continental (Argus Cyber Security)
- Arm Limited
- Guardknox Cyber Technologies Ltd.
- Vector Informatik GmbH
- Karamba Security
- Synopsys
- Upstream Security
- Sectigo Limited
- ESCRYPT
- RunSafe Security, Inc.
- Trend Micro
- Harman International
- Trillium Secure Inc.
- STMicroelectronics
- Infineon Technologies AG
- NXP Semiconductors
- Bosch Mobility Solutions
- Microchip Technology
- Aptiv
- Irdeto
- Other Market Players
Frequently Asked Questions
The Automotive Cybersecurity market is estimated to be valued at US$ 4,050.3 Mn in 2026.
Rapid increase in connected and autonomous vehicles is the key demand driver for Automotive Cybersecurity market
In 2026, Asia Pacific region dominates the market with ~37% share in the global Automotive Cybersecurity market.
Among Application, the telematics segment is expected to grow rapidly at 17.4% CAGR from 2026 to 2033.
Continental (Argus Cyber Security), Arm Limited, Guardknox Cyber Technologies Ltd., Vector Informatik GmbH, Karamba Security, and Synopsys are the leading players in the Automotive Cybersecurity market.








