- Hardware & Software IT Services
- Hardware Security Modules Market
Hardware Security Modules Market Size, Share, and Growth Forecast, 2026 - 2033
Hardware Security Modules Market by Module Type (LAN-Based / Network-Attached HSMs, PCIe-Based (Internal) HSMs, USB-Based / Portable HSMs, Cloud-Based HSMs), Deployment Mode (On-Premises, Cloud), Organization Size (Large Enterprises, Small & Medium Enterprises (SMEs)), Application (Payment Processing & Transaction Security, Authentication & Access Control, Public Key Infrastructure (PKI) & Certificate Management, Data & Database Encryption, IoT Device Identity & Security, Code Signing & Software Integrity, Others), Industry, and Regional Analysis for 2026 - 2033
Hardware Security Modules Market Size and Trends Analysis
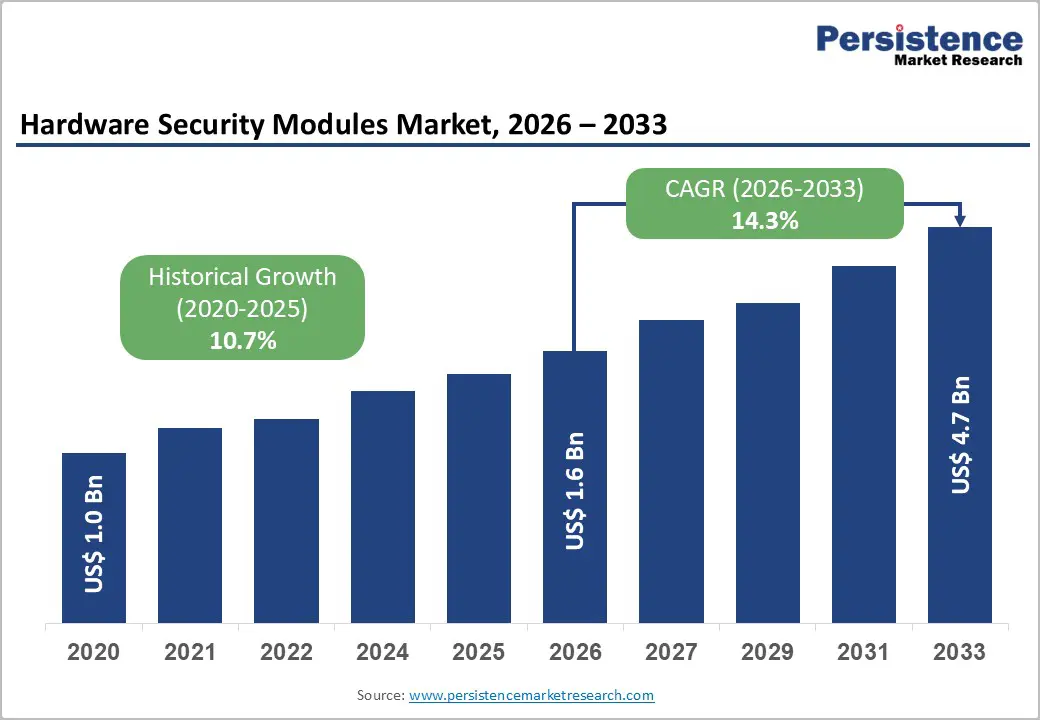
The global hardware security modules market size is likely to be valued at US$ 1.8 billion in 2026 and is projected to reach US$ 4.7 billion by 2033, growing at a CAGR of 14.3% between 2026 and 2033.
This robust expansion reflects heightened enterprise demand for cryptographic key protection infrastructure, driven by regulatory compliance intensification, cloud infrastructure modernisation, and the emerging quantum computing threat requiring cryptographic algorithm transition.
The Market demonstrates particularly strong momentum in financial services, government, and healthcare sectors, where sensitive data protection and regulatory mandates create compelling economic justification for HSM adoption across hybrid and cloud-native environments.
Key Industry Highlights:
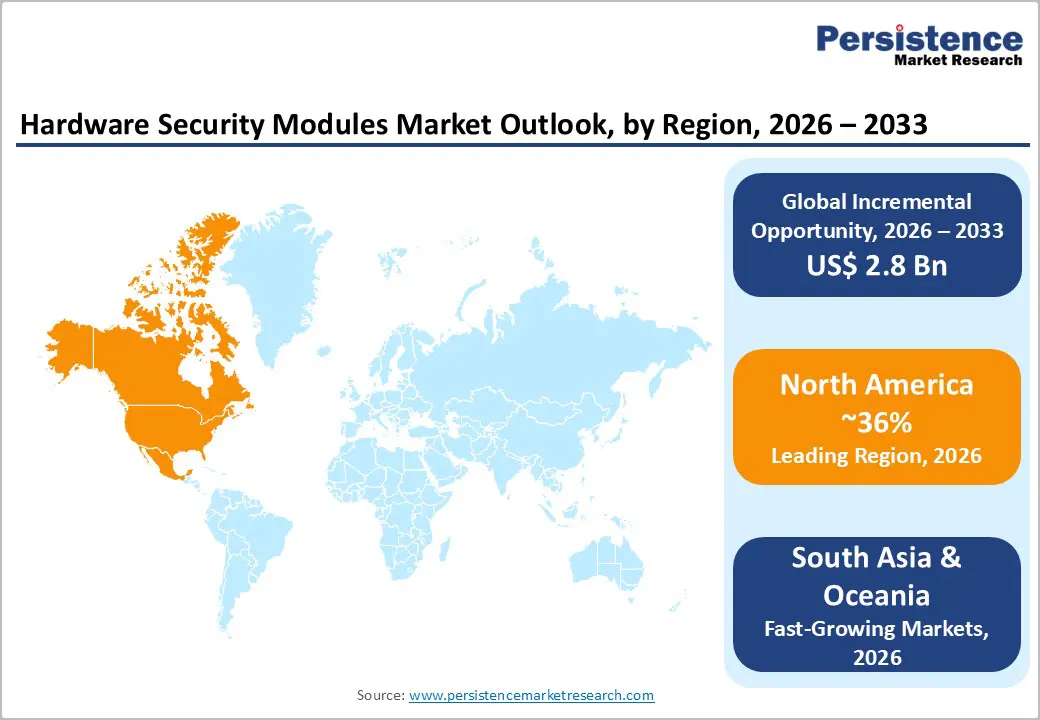
- Regional Leadership: North America leads the global Hardware Security Modules (HSM) market with ~36% share, supported by strong PCI DSS enforcement, NIST-led cryptographic standards, high BFSI digitalisation, and early adoption of post-quantum–ready security infrastructure.
- High-Growth Asian Markets: East Asia holds ~21% share and represents the fastest-growing regional market, driven by rapid BFSI expansion, large-scale e-government adoption, IoT and 5G rollout, and strict data residency mandates across China, Japan, and South Korea.
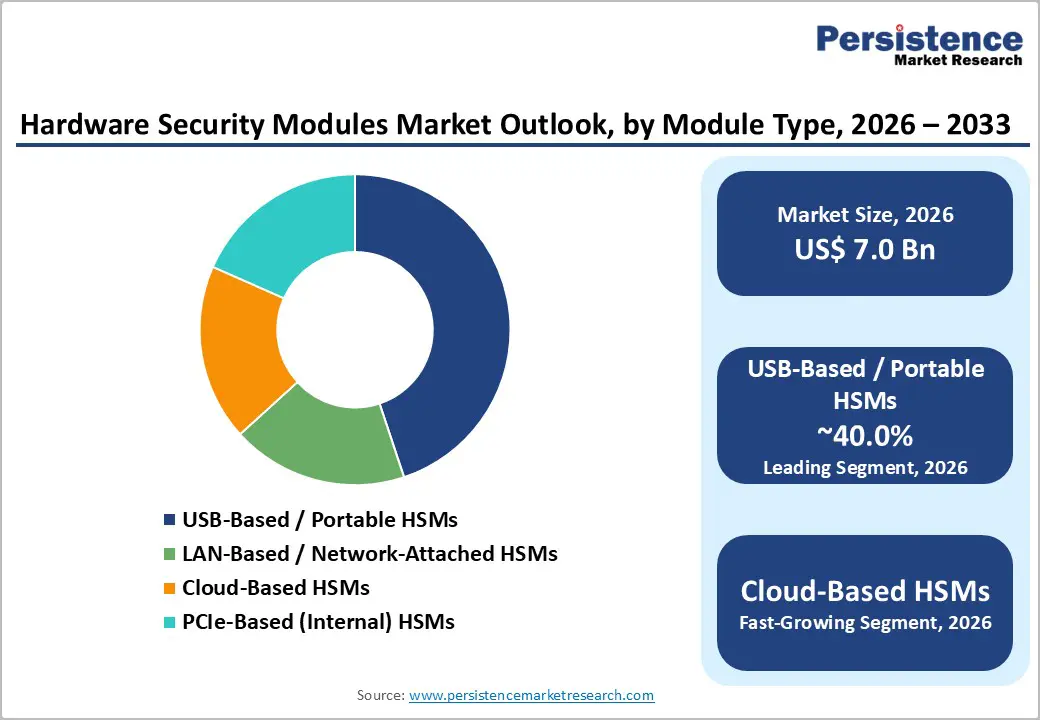
- Leading Products: USB-Based / Portable HSMs dominate the market with the largest share, reflecting long-standing demand for flexible, field-deployable cryptographic solutions among distributed enterprises and smaller organisations.
- Fastest-Growing Product Type: Cloud-Based HSMs are the fastest-growing segment, fueled by cloud migration, HSM-as-a-Service adoption, hyperscaler integrations, and the shift from CapEx-heavy on-premises models to scalable OpEx-based security solutions.
| Key Insights | Details |
|---|---|
| Hardware Security Modules Market Size (2026E) | US$ 1.8 Bn |
| Market Value Forecast (2033F) | US$ 4.7 Bn |
| Projected Growth (CAGR 2026 to 2033) | 14.3% |
| Historical Market Growth (CAGR 2020 to 2025) | 10.7% |
Market Dynamics
Drivers - Post-Quantum Cryptography Standardisation and Mandatory Migration Timeline
The Hardware Security Modules Market is experiencing fundamental transformation driven by the accelerating quantum computing timeline and NIST's standardisation of post-quantum cryptography (PQC) algorithms. The National Institute of Standards and Technology has declared that RSA, EdDSA, and ECDH digital signature algorithms will be deprecated by 2030 and disallowed after 2035, establishing a mandatory migration deadline that forces enterprises to redesign cryptographic infrastructure across all digital asset categories.
Leading HSM vendors including Crypto4A, Entrust, Marvell, Utimaco, and Thales, are prioritising crypto-agile architectures that support both classical cryptographic algorithms and emerging post-quantum alternatives, enabling organisations to transition at a controlled pace while maintaining legacy system compatibility. The challenge confronting the Hardware Security Modules Market is that most HSM vendors currently offer only external PQC support, with very few having redesigned underlying hardware and firmware architectures for quantum-resistant operations; only Crypto4A has commercially launched HSMs with genuinely quantum-safe internal architecture.
Organizations in highly sensitive verticals, such as government, critical infrastructure, and financial services, are accelerating HSM procurement decisions to establish quantum-resistant foundations before the 2035-2040 mandatory transition window, directly driving Hardware Security Modules Market expansion through 2033. The post-quantum transition represents a multi-trillion-dollar infrastructure upgrade across global enterprises, with HSMs serving as the foundational trust anchor for all cryptographic operations.
Regulatory Compliance, Proliferation, and Financial Sector Digitalisation
Regulatory bodies globally have substantially hardened cybersecurity and cryptographic control requirements, establishing Hardware Security Modules as mandatory infrastructure for financial services, government, and healthcare organisations. The Payment Card Industry Data Security Standard (PCI DSS) mandates HSM deployment for all payment card processing, requiring FIPS 140-2 Level 3 certification minimum for hardware-based key protection and cryptographic operations.
The European Union's regulatory framework, including GDPR, Payment Services Directive 2 (PSD2), and SWIFT compliance requirements, establishes strict data residency, key management, and incident reporting obligations that most organisations address through enterprise-grade HSM infrastructure.
India's banking sector, experiencing extraordinary BFSI growth (expanding from INR. 1,80,000 crores in 2005 to INR. 91,00,000 crores by 2025, now contributing 27% to GDP), has mandated cryptographic key protection standards aligned with RBI (Reserve Bank of India) and SEBI (Securities and Exchange Board of India) frameworks, directly driving HSM adoption across Indian financial institutions.
Restraint - Complexity of Crypto-Agile Architecture Implementation and Certification Delays
While regulatory mandates create demand for quantum-safe HSM solutions, the practical challenge of transitioning HSM architecture from classical to post-quantum cryptography introduces substantial implementation complexity and cost barriers. Current FIPS 140-2 and FIPS 140-3 certification standards do not mandate quantum-safe internal architecture, removing regulatory incentive for vendors to undertake expensive redesign of firmware, boot processes, and key management protocols incorporating post-quantum algorithms.
Organisations deploying new HSM solutions discover limited availability of production-grade quantum-safe alternatives, creating procurement delays and forcing decisions between classical-algorithm HSMs with uncertain quantum-ready upgrade pathways versus next-generation solutions with higher initial costs and uncertain long-term supportability. This certification gap and vendor capability variation constrain market growth by extending HSM procurement cycles and introducing evaluation complexity that delays purchase decisions, particularly among mid-market organisations with limited cryptographic expertise.
Opportunity - IoT Device Identity and Edge Cryptographic Security
Internet of Things infrastructure expansion is creating substantial demand for Hardware Security Modules integrated into device identity management, edge computing gateways, and distributed authentication systems. As global internet usage reaches 6 billion users (74% of the world population) in 2025, up from 60% in 2020, with critical infrastructure and industrial systems becoming increasingly connected and remote-managed, the requirement for device-level cryptographic identity and tamper-resistant key protection has become foundational to operational security.
The Market is positioning IoT device identity and security as the fastest-growing application segment, driven by organizations requiring secure device provisioning, certificate lifecycle management, and edge-based cryptographic operations across distributed IoT deployments spanning manufacturing, energy, transportation, and smart city infrastructure. IoT Device Identity & Security applications require different HSM architectures, distributed key management, lightweight cryptographic protocols, and edge computing integration compared to traditional centralised Payment Processing HSMs, creating opportunities for HSM vendors to develop specialised product portfolios addressing IoT-specific requirements.
Organisations deploying thousands or millions of connected devices face critical challenges in managing device certificates, rotating cryptographic keys, and ensuring tamper-resistant device authentication at the edge, with solutions increasingly integrated into hardware security modules deployed alongside IoT gateways and edge computing infrastructure.
Post-Quantum Cryptography Transition Services and Crypto-Agile Platform Leadership
Hardware Security Modules vendors capable of establishing credibility in post-quantum cryptography transition services and delivering truly crypto-agile platforms are positioned to capture substantial market share during the 2026-2033 mandate transition period. The quantum computing threat timeline, with cryptographically relevant quantum computers expected around 2035-2040, creates a multi-year window for organisations to evaluate, pilot, and deploy crypto-agile HSM solutions capable of supporting both classical and post-quantum algorithms through hybrid deployment models.
Organisations in critical infrastructure, government, and high-security financial services are increasingly issuing requests for proposals explicitly requiring post-quantum readiness, crypto-agility, and vendor roadmaps for complete quantum-safe architecture transition by 2032-2033. This creates substantial opportunities for HSM vendors establishing early leadership in post-quantum commercialisation and providing comprehensive transition services (cryptographic algorithm assessment, legacy system compatibility analysis, phased deployment planning) that help enterprises navigate the complex quantum migration journey.
Recent strategic developments underscore market momentum: Utimaco launched the CSe-Series HSM with post-quantum readiness, Eviden launched PQC HSMaaS with EU sovereign standards, and JISA Softech launched India's first indigenously developed Payment HSM with post-quantum readiness, indicating vendor recognition of quantum-safe positioning as a critical market differentiator. Organisations seeking to establish quantum-resistant cryptographic foundations before regulatory mandates take effect represent a substantial opportunity for Hardware Security Modules vendors capable of demonstrating technical credibility and deployment experience in quantum-safe transitions.
Category-wise Analysis
Module Type Insights
USB-Based and Portable Hardware Security Modules maintain market dominance with 40% market share in 2026, reflecting significant adoption among organisations requiring portable, field-deployable cryptographic capabilities and users needing flexibility in accessing cryptographic functions across multiple locations. Portable HSMs address use cases including mobile workforce authentication, remote office cryptographic operations, and scenarios where centralized HSM infrastructure is unavailable or impractical.
The segment's market leadership reflects historical preference for HSM portability among individual security professionals, smaller organisations, and distributed enterprises lacking centralised IT infrastructure. The portable HSM market share is gradually declining as organisations shift toward centralised, cloud-based key management architectures that provide superior auditability, access control, and disaster recovery capabilities compared to portable, mobile devices.
Cloud-Based Hardware Security Modules represent the fastest-growing HSM category, driven by cloud infrastructure adoption and digital transformation initiatives requiring cryptographic key management integrated with hyperscaler cloud platforms. Cloud-based HSMs address the capital expenditure barrier that historically constrained mid-market adoption, enabling organisations to access enterprise-grade cryptographic capabilities through operational expense models aligned with cloud service consumption patterns.
Industry Insights
The BFSI sector commanded approximately 42% of the Hardware Security Modules Market in 2026, reflecting regulatory mandates, transaction criticality, and substantial cryptographic key management requirements across banking infrastructure, insurance operations, and financial services platforms. India's BFSI sector demonstrates exceptional growth dynamics, expanding from Rs. 1,80,000 crore (US$ 20.28 billion) in 2005 to Rs. 91,00,000 crore (US$ 1 trillion) in 2025, now contributing 27% to national GDP, with improved fundamental metrics (gross NPAs declining from 5.8% in FY22 to 2.2% in FY25) indicating sector stability and capacity for IT infrastructure investment.
Europe's BFSI sector (€0.9 trillion value added, 5 million employees) and China's banking sector, which accounts for RMB 467.3 trillion in assets, are growing 7.9% annually. represent substantial Hardware Security Modules markets where regulatory compliance, transaction security, and payment system modernisation drive sustained HSM procurement. The BFSI sector's dominance reflects historical concentration of cryptographic key management requirements, payment processing criticality, and regulatory examination emphasis on encryption control that creates structural demand for Hardware Security Modules across all significant financial institutions.
The IT & Telecom sector represents the fastest-growing end-use industry for Hardware Security Modules, driven by digital transformation initiatives, cloud infrastructure expansion, and the emergence of telecommunication network security requirements. India's telecom sector, which has 1.21 billion subscribers, 86.09% tele-density, gross revenue US$ 43.42 billion in FY25, is undergoing substantial modernization including 5G network rollout, contributing 25% of wireless data usage in FY25, BharatNet fibre expansion (2.13 lakh Gram Panchayats service-ready), and emerging security requirements around network function virtualisation and cloud-native telecom infrastructure.
Regional Insights and Trends
North America Hardware Security Modules Market Trends
North America commands 36% of the global hardware security modules market, reflecting organisational maturity in cryptographic governance, substantial BFSI sector investment, and regulatory framework density driving HSM adoption. The region's HSM market is propelled by PCI DSS compliance mandates for payment processing, SEC cybersecurity disclosure requirements creating board-level accountability for data protection, and NIST standards leadership establishing cryptographic best practices that organisations globally reference. The North American market is characterised by sophisticated procurement cycles emphasising post-quantum readiness, cloud HSM integration capabilities, and compliance certification (FIPS 140-3 Level 3 validation), with technology leaders prioritising vendors demonstrating quantum-safe architecture maturity and roadmaps toward mandatory 2035-2040 cryptographic algorithm transitions.
Large financial institutions in North America are substantially increasing HSM investments to support digital transformation initiatives, real-time payment infrastructure modernisation, and emerging cloud security requirements. Mid-market organisational HSM adoption in North America remains constrained by cost sensitivity and competing IT budget priorities, though cloud-based HSM services are enabling SMB penetration by reducing capital expenditure barriers.
East Asia Hardware Security Modules Market Trends
East Asia represents 21% of the global hardware security modules market, with particularly strong growth trajectories driven by rapid BFSI sector expansion, government digital transformation initiatives, and emerging IoT and 5G infrastructure requiring cryptographic security.
China's banking and insurance sectors demonstrate robust growth, with banking assets at RMB 467.3 trillion growing 7.9% YoY as of Q2 2025, insurance assets RMB 39.2 trillion growing 9.2% annually, with 1.029 billion+ online payment users and 1.004 billion+ e-government users creating substantial cryptographic key management requirements across payment processing and digital government infrastructure. Data residency mandates under China's Cybersecurity Law and Data Security Law require localised HSM operations, creating opportunities for vendors capable of deploying on-shore infrastructure while restricting international managed service providers, effectively fragmenting the East Asian market among regional vendors and global companies with localised operations.
East Asia remains the fastest-growing regional hardware security modules market, driven by the BFSI sector digitalisation and regulatory mandate acceleration requiring cryptographic key management infrastructure deployment across financial systems.
Europe Hardware Security Modules Market Trends
Europe accounts for 24% of the global share, with growth constrained by organizational preference for in-house key management in large enterprises, strict data sovereignty regulations, and competitive intensity among European HSM vendors. GDPR compliance requirements, NIS2 Directive mandates, and payment services regulations (PSD2, SEPA compliance) create regulatory drivers for HSM adoption across organisations handling payment systems and personal data.
Recent vendor developments reflect European market dynamics: Eviden (Atos Group) launched PQC HSMaaS with full EU sovereign standards compliance and NIS2 alignment (October 2024), positioning the company to capture European demand for sovereign, quantum-safe cryptographic solutions meeting strict regulatory requirements. Europe's Hardware Security Modules market is characterized by emphasis on data residency, regulatory compliance, and sovereign security positioning rather than cost minimization, creating opportunities for vendors capable of meeting stringent European regulatory and data protection requirements.
Competitive Landscape
The global Hardware Security Modules (HSM) market demonstrates a moderately consolidated and oligopolistic structure, where a limited number of global players hold a strong revenue share while several regional and niche companies operate alongside them. Thales Group dominates the market due to its comprehensive portfolio spanning payment, general-purpose, and cloud HSMs with strong regulatory certifications. IBM Corporation, Entrust, Utimaco, Futurex, and Atos (Eviden) are other key players, benefiting from deep enterprise relationships and high trust in regulated industries such as BFSI and government.
Competition is primarily driven by product reliability, compliance with FIPS and PCI standards, and secure cloud-based HSM offerings. Although large vendors control a substantial portion of global revenues, emerging players focusing on HSM-as-a-Service, post-quantum cryptography, and API-driven architectures continue to intensify competition. Overall, the market remains innovation-led with high entry barriers due to certification, security, and trust requirements.
Key Industry Developments
- On August 18, 2025, Marvell Technology, Inc. announced that Microsoft selected Marvell LiquidSecurity HSMs to power Azure Cloud HSM, expanding support for cloud-based, single-tenant cryptographic key management. The PCIe-based HSMs enable high-density, multi-tenant cloud environments with FIPS 140-3 Level 3 compliance, enhancing secure key management, encryption, and PKI services while supporting scalable, energy-efficient cloud deployments.
- On October 8, 2024, Eviden (Atos Group) launched PQC HSMaaS, a post-quantum-ready, EU sovereign Hardware Security Module as a Service, powered by the Trustway Proteccio™ brand. The solution provides the highest security certification under ANSSI standards, ensures NIS2 compliance, and offers cloud-independent, fully sovereign management of sensitive data, positioning Eviden as a key provider in the secure HSMaaS market.
Companies Covered in Hardware Security Modules Market
- Thales
- Utimaco Management Services GmbH
- Futurex
- Alfresco Software, Inc.
- Box, Inc.
- DocuWare Corporation
- Hyland Software, Inc.
- International Business Machines Corporation
- Laserfiche
- M-Files Corporation
- Microsoft
- OpenText Corporation
- Oracle
Frequently Asked Questions
The global hardware security modules market is projected to be valued at US$ 1.8 Bn in 2026.
The USB-Based / Portable HSMs segment is expected to account for approximately 40% of the Global Hardware Security Modules Market by Module Type in 2026.
The market is expected to witness a CAGR of 14.3% from 2026 to 2033.
The Hardware Security Modules market growth is driven by mandatory post-quantum cryptography migration timelines, tightening global regulatory compliance (PCI DSS, GDPR, NIS2, RBI/SEBI), and accelerating digitalisation of BFSI, government, and critical infrastructure requiring hardware-backed, quantum-ready cryptographic key protection.
The Hardware Security Modules market presents strong opportunities in securing large-scale IoT and edge deployments and in providing crypto-agile, post-quantum-ready HSM platforms and transition services ahead of mandatory global PQC migration deadlines.
Key players in the Hardware Security Modules Market include Thales, Utimaco, Entrust, Marvell Technology, Futurex, and Eviden (Atos Group).







