- Hardware & Software IT Services
- End-point Security Market
End-point Security Market Size, Share, and Growth Forecast, 2026 – 2033
End-point Security Market by Component (Solution [Firewall, Antivirus / Anti-malware, Endpoint Detection & Response (EDR), Extended Detection & Response (XDR), Patch Management, Others], Services [Professional Services, Managed Services]), Deployment (On-Premises, Cloud / SaaS), Endpoint Type, Industry, and Regional Analysis for 2026 – 2033
End-point Security Market Size and Trends
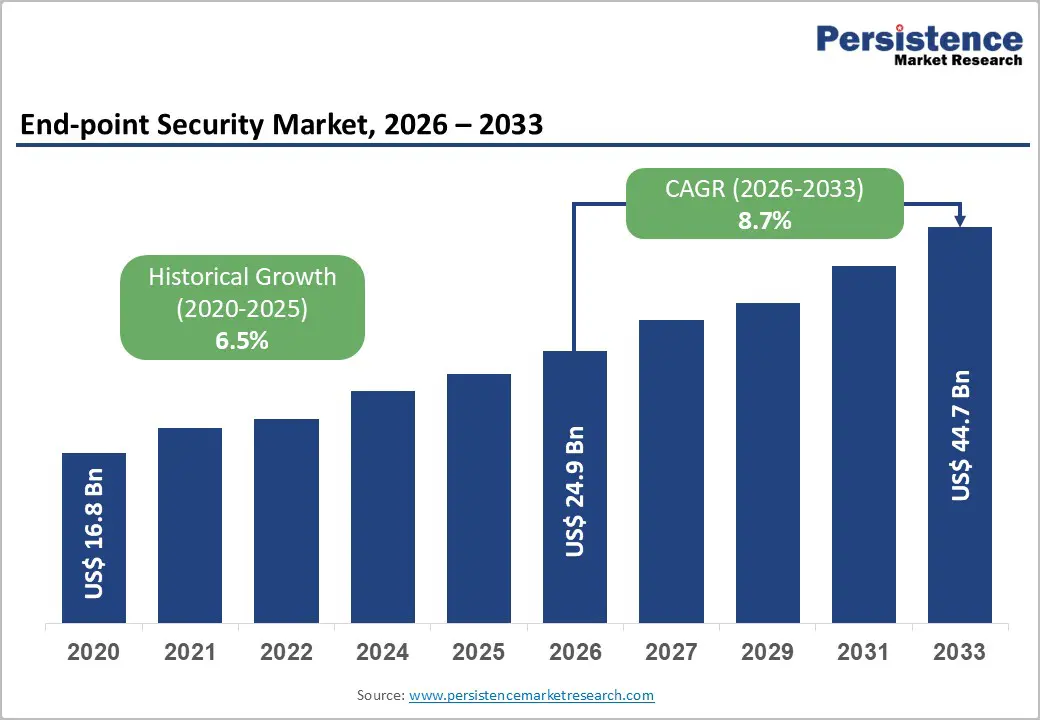
The global End-point Security Market size is projected to rise from US$24.9 Bn in 2026 to US$44.7 Bn by 2033. It is anticipated to witness a CAGR of 8.7% during the forecast period from 2026 to 2033, driven by the escalating sophistication and frequency of cyberattacks targeting enterprise endpoints, the accelerated adoption of remote and hybrid work models that have exponentially increased the number and diversity of devices requiring protection, and stringent regulatory compliance mandates across industries requiring robust security measures.
Key Industry Highlights
- Leading Component: Antivirus / Anti-malware remains the largest solution segment, capturing over 27% market share in 2026 and valued at more than US$ 6.7 Bn, as it provides essential baseline protection against prevalent threats such as ransomware, trojans, and viruses across all endpoint types. Extended detection & response (XDR) is the fastest-growing solution, driven by the need for unified threat visibility, faster correlation across endpoints, networks, and automated response amid rising attack complexity and cybersecurity skill shortages.
- Leading Deployment: On-Premises leads with over 44% market share in 2026, valued at more than US$ 11 Bn, supported by data sovereignty, regulatory compliance, and deep integration requirements in sectors such as BFSI and government. Cloud / SaaS is the fastest growing, registering a 13.9% CAGR, driven by scalability, rapid rollout for remote workforces, centralized management, and lower upfront infrastructure costs.
- Leading Endpoint Type: Workstations dominate with over 40% market share in 2026, exceeding US$ 10 Bn, as they support mission-critical enterprise workloads and store high-value intellectual property, making them prime ransomware targets. Mobile devices are the fastest-growing endpoint type, fueled by BYOD adoption, remote work expansion, and rising mobile-specific threats such as phishing, malware, and credential theft.
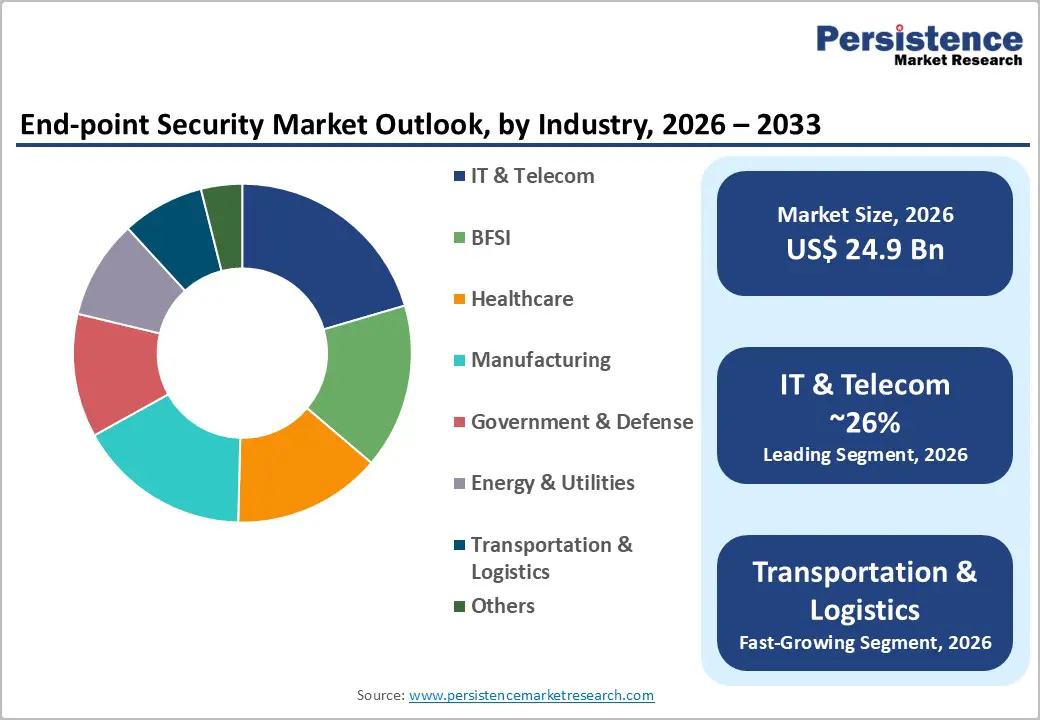
- Leading Industry: IT & Telecom holds the largest industry share at over 26% in 2026, valued at more than US$ 6.5 Bn, due to massive endpoint volumes, high data sensitivity, cloud adoption, and strict compliance requirements. Transportation & Logistics is among the fastest-growing industries, driven by rapid digitization of fleets and supply chains, increased ransomware risk, and the critical need to avoid operational downtime.
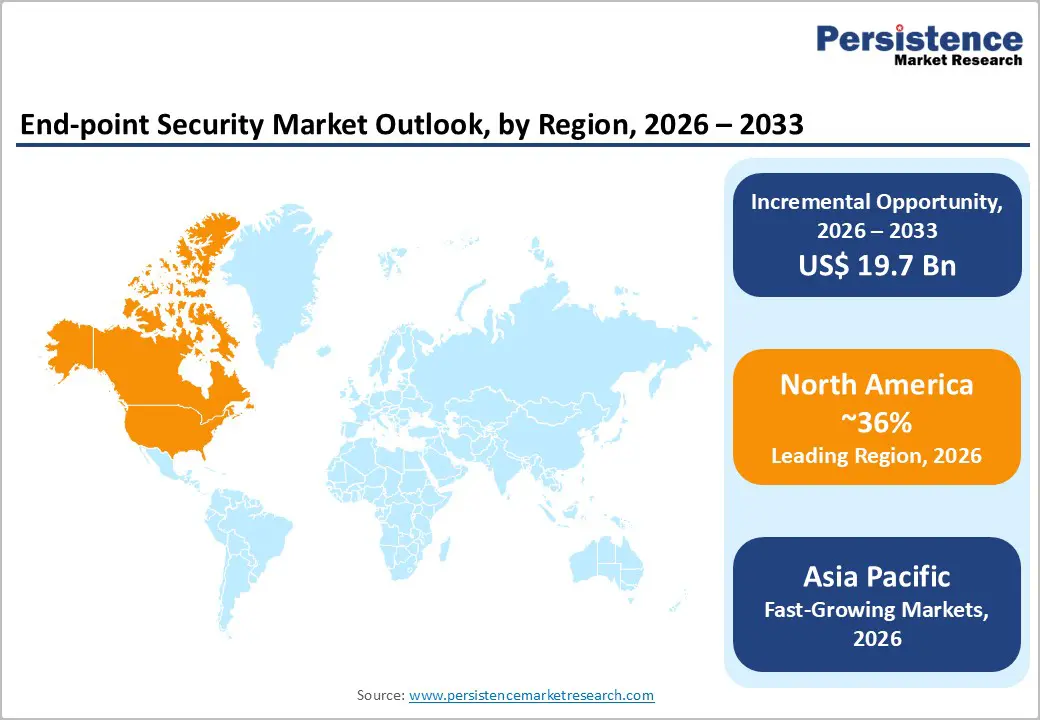
- Leading Region: North America leads the global endpoint security market with over 36% share in 2026, reaching approximately US$ 9.0 Bn, supported by advanced infrastructure, high ransomware exposure, and strong regulatory enforcement. Asia Pacific is the fastest-growing region with a 14.1% CAGR, driven by manufacturing expansion, government-led digital initiatives, cloud-first strategies, and rising endpoint adoption across IT, OT, and IoT environments.
| Report Attribute | Details |
|---|---|
|
End-point Security Market Size (2026E) |
US$24.9 Bn |
|
Market Value Forecast (2033F) |
US$44.7 Bn |
|
Projected Growth (CAGR 2026 to 2033) |
8.7% |
|
Historical Market Growth (CAGR 2020 to 2025) |
6.5% |
Market Dynamics
Driver
Rising Sophistication of Ransomware and Advanced Persistent Threats
The endpoint security market is accelerating due to the growing sophistication and frequency of ransomware and APT attacks. Between January and September 2025, organizations globally experienced 4,701 ransomware incidents, a 46% increase compared to the same period in 2024. 50% of these attacks targeted critical infrastructure sectors such as manufacturing, healthcare, energy, and transportation, with manufacturing witnessing a 61% YoY surge, disrupting supply chains and operations. This escalation has forced the industry to significantly increase endpoint security spending due to heightened targeting and strict regulatory requirements for breach notification and forensic investigations. Threat actors are also shifting from encryption-based attacks to extortion-only tactics, rising from 3% in 2024 to 10% in 2025, pushing organizations to deploy proactive detection and response capabilities.
Proliferation of Remote Work, BYOD, and Distributed Endpoints
The shift to hybrid and remote work has dramatically expanded the endpoint attack surface, as organizations now manage a wide variety of devices across untrusted networks. With over 80% of firms adopting BYOD and nearly half increasing BYOD due to remote work, personal devices such as smartphones and tablets are heavily used for business tasks, increasing vulnerability. IT teams report that BYOD negatively impacts security posture, and personal devices are statistically more prone to malware than corporate endpoints. This has driven strong demand for endpoint security solutions that can protect distributed endpoints across home networks and remote environments.
Restraint
Implementation Complexity and Legacy System Integration Challenges
Organizations face significant technical and operational hurdles when implementing endpoint security across complex IT landscapes that include legacy systems, multiple operating systems, mobile devices, and IoT endpoints. High dependency on kernel-level components increases the risk of system instability, as highlighted by the July 2024 CrowdStrike outage caused by a faulty Windows update. Such incidents have driven platform vendors like Microsoft to rethink endpoint–kernel interactions, increasing scrutiny on security agent design and deployment practices. Enterprises are now compelled to adopt rigorous testing, validation, and staged rollout processes to avoid business disruptions. These extended deployment cycles raise implementation time and total cost of ownership.
Shortage of Skilled Cybersecurity Professionals
The endpoint security market is constrained by a widespread shortage of skilled cybersecurity professionals who can implement, manage, and optimize advanced security solutions. This talent gap forces many organizations to delay deployments, maintain weak configurations, and experience gaps in threat detection and response. As a result, enterprises increasingly rely on managed security services and automation platforms, shifting demand toward outsourced and cloud-based solutions. The shortage also limits SME adoption, as smaller firms lack dedicated security teams and cannot justify high staffing costs.
Opportunity
Zero Trust Architecture Adoption
Zero trust architecture (ZTA) adoption is accelerating demand for advanced endpoint security as endpoints become the primary enforcement point for never trust, always verify policies. With users accessing applications from unmanaged devices and remote locations, organizations need continuous endpoint authentication, posture assessment, and behavioral monitoring. Real-time visibility into device health, identity, and activity becomes essential to enable least privilege access. Integration of endpoint security with identity, cloud, and access controls creates demand for unified platforms. As Zero Trust emphasizes continuous verification, AI-driven threat detection, and automated response at the endpoint gain importance. This transition expands endpoint security from basic malware protection to a strategic control layer in enterprise security architecture.
?AI-Driven Intelligence & Shift to Cloud-Native & Managed Solutions
The integration of AI and machine learning is transforming endpoint security by enabling real-time threat detection, behavioral analysis, and predictive response to zero-day and fileless attacks, reducing reliance on signature-based methods. ML models continuously learn from endpoint telemetry, improving accuracy and lowering false positives across diverse devices. The shift to cloud-native and managed endpoint security solutions allows organizations to secure remote and hybrid workforces with centralized visibility and policy enforcement. Managed endpoint security services further address cybersecurity skill shortages by providing 24/7 monitoring and response.
Category-wise Analysis
Component Analysis,
Antivirus / Anti-malware dominates the solution segment, capturing more than 27% market share in 2026 with a value exceeding US$ 6.7 Bn, as they provide essential first-line defense against a wide range of threats such as viruses, ransomware, and trojans, which remain the most common attack vectors. They are universally required across all devices to detect, quarantine, and remediate malicious code in real time. With the increasing frequency of remote work and device diversity, these solutions are critical for baseline protection. Their broad adoption is driven by the ongoing need to prevent compromise and maintain operational continuity.
Extended detection & response (XDR) demonstrate highest growth due to organizations' need for unified visibility across endpoints, networks, email, and cloud to detect complex attacks that evade single-point tools. As cyber threats become more sophisticated, teams require faster threat correlation and automated response to reduce dwell time and minimize damage. XDR’s ability to combine telemetry from multiple sources into one platform helps security teams prioritize alerts and act quickly. The growing shortage of skilled cybersecurity professionals makes XDR’s automation and orchestration essential for effective threat management.
Deployment Analysis,
On-Premises dominate the market, capturing over 44% market share in 2026 with a value exceeding US$ 11 Bn, due to many organizations still preferring to keep sensitive security controls and threat intelligence within their own infrastructure to maintain full control and reduce exposure. It is especially important for industries with strict compliance and data residency requirements, such as BFSI and government. On-premises solutions also offer faster response and deeper integration with existing enterprise systems, enabling tighter policy enforcement. Organizations with large legacy environments often find on-premises deployment easier to manage and customize to their specific security workflows.
Cloud / SaaS demonstrates the highest growth with a CAGR of 13.9% due to organizations' need for rapid, scalable protection without heavy on-premises infrastructure. SaaS solutions allow quick rollouts across remote and hybrid workforces, ensuring consistent security policies and real-time threat updates. They also reduce IT burden by handling maintenance, patching, and upgrades centrally. Subscription-based pricing makes it easier for businesses of all sizes to adopt advanced endpoint protection without high upfront costs.
Endpoint Type Analysis,
Workstations hold over 40% of the market share in 2026, with a value exceeding US$ 10 Bn, as they are widely used across enterprises for critical, high-value tasks such as engineering, design, data analysis, and software development, making them prime targets for cyberattacks. These systems often store sensitive intellectual property and access corporate networks, requiring stronger protection. Workstations typically run multiple complex applications and handle large datasets, increasing exposure to malware and ransomware. Organizations therefore prioritize advanced endpoint security on workstations to ensure business continuity, regulatory compliance, and protection of high-impact assets.
Mobile devices are expected to grow at the highest rate as they are increasingly used for critical work tasks, including email, collaboration, and access to corporate apps, making them prime targets for cyberattacks. The rise of remote and hybrid workforces has expanded the attack surface, with employees accessing sensitive data from personal and public networks. Mobile apps often store credentials and corporate data, increasing the need for strong authentication and secure app management. With growing threats like mobile malware, phishing, and device theft, organizations must invest more in mobile-specific endpoint protection to prevent breaches and ensure compliance.
Industry Analysis,
IT & Telecom commands the largest market share at over 26% in 2026, with a value exceeding US$ 6.5 Bn, due to these sectors managing massive networks with thousands of endpoints, making them prime targets for cyberattacks. They also handle highly sensitive customer and business data, requiring strong protection against malware, ransomware, and unauthorized access. With rapid digital transformation, remote work, and cloud adoption, IT & Telecom firms need continuous endpoint monitoring and threat prevention. Strict regulatory and compliance requirements push these organizations to invest heavily in advanced endpoint security solutions.
Transportation & logistics is expected to grow at a significant rate as this industry is rapidly digitizing operations across fleets, warehouses, and supply chains, creating many new endpoints that need protection. With increasing reliance on connected systems for route optimization, tracking, and real-time inventory, the risk of ransomware and cyberattacks rises sharply. Many logistics companies operate 24/7, meaning any downtime due to an endpoint breach directly impacts delivery timelines and customer trust. Stricter regulations and the need to protect customers and shipment data are forcing the sector to adopt stronger endpoint security measures at a faster pace.
Regional Insights
North America End-point Security Market Trends
North America accounts for over 36% of the End-point Security market share in 2026, reaching approximately US$ 9.0 Bn, driven by advanced infrastructure, high cloud adoption, remote work, and strong regulatory requirements. The region is a major innovation hub for next-generation solutions such as XDR, EDR, and managed security services. The United States is a prime target for ransomware attacks due to its large digital economy, prompting organizations to strengthen endpoint defenses. Financial institutions, healthcare, and government agencies are prioritizing endpoint security to meet compliance needs and build cyber resilience. Large enterprises continue to push market sophistication through analytics, threat intelligence integration, and automated response capabilities.
Asia Pacific End-point Security Market Trends
Asia Pacific is expected to grow at the highest rate with a CAGR of 14.1%, led by China, where strong manufacturing growth, digital transformation, and the Made in China 2025 policy drive cybersecurity self-reliance and high endpoint protection adoption. India is emerging rapidly due to Digital India initiatives, large internet penetration, growing e-commerce and remote work, and mandatory RBI endpoint security requirements. Japan retains a significant market share due to advanced tech adoption, strict regulations, and extensive use of AI-driven security tools. The region is rapidly shifting toward cloud-based endpoint security as organizations adopt cloud-first strategies and remote working norms, supported by data protection laws. The surge in IoT devices expands attack surfaces, boosting demand for endpoint security across diverse devices and OT systems.
Europe End-point Security Market Trends
Europe is expected to hold more than 23% share by 2026, driven by strict regulatory mandates such as GDPR and the NIS Directive, which enforce heavy compliance requirements and penalties. Germany leads the region, supported by its strong industrial base, advanced infrastructure, and significant government cybersecurity funding, with widespread adoption of AI-driven endpoint solutions. France is also expanding rapidly due to major national cybersecurity investments and stringent sector-specific security mandates in aerospace, energy, and critical infrastructure. The UK and Spain are emerging as key growth markets due to accelerated digital transformation and rising ransomware incidents.
Competitive Landscape
The end-point security market is moderately fragmented, with several established players and emerging specialists competing across various industry segments. Companies are differentiating themselves by focusing on advanced threat detection (using AI/ML), integrated security platforms, and seamless scalability to capture the diverse needs of their customers. They increasingly offer subscription-based and SaaS models to strengthen recurring revenue and customer stickiness. Strategic alliances and partnerships with cloud providers and MSPs help expand market reach. Ongoing R&D investments and targeted acquisitions fuel innovation and broaden product portfolios to stay ahead of evolving cyber threats.
Key Industry Developments
- In November 2025, LevelBlue completed the acquisition of Cybereason, strengthening its leadership in managed detection and response (MDR) and expanding its endpoint security capabilities through Cybereason’s advanced XDR platform. The deal also brings enhanced DFIR, threat intelligence, and AI-driven security services, while attracting new investments from SoftBank and Liberty Strategic Capital.
- In February 2025, CrowdStrike launched CrowdStrike Falcon Identity Protection for Microsoft Entra ID, providing unified prevention, detection, and response against identity-based attacks across hybrid environments. The solution enhances protection against sophisticated threats targeting cloud identity services, combining inline prevention with advanced identity threat detection and response to secure both cloud and on-premises systems.
Companies Covered in End-point Security Market
- Microsoft Corporation
- CrowdStrike Holdings, Inc.
- SentinelOne, Inc.
- Trend Micro Incorporated
- Palo Alto Networks, Inc.
- Cisco Systems, Inc.
- Fortinet, Inc.
- Broadcom Inc.
- BlackBerry Limited
- Check Point Software Technologies Ltd.
- Sophos Group plc
- McAfee LLC
Frequently Asked Questions
The global market is projected to be valued at US$24.9 Bn in 2026.
Growing regulatory pressure and the rising sophistication of cyber threats force organizations to adopt stronger endpoint protection to secure data and ensure business continuity, is a key driver of the market.
The market is expected to witness a CAGR of 8.7% from 2026 to 2033.
Rising adoption of AI-driven and behavioral-based threat detection, and the increasing shift toward unified security platforms that provide better visibility and faster response, are creating strong market expansion potential.
Microsoft Corporation, CrowdStrike Holdings, Inc., SentinelOne, Inc., Trend Micro Incorporated, Palo Alto Networks, Inc., Cisco Systems, Inc. are among the leading key players.








