- Hardware & Software IT Services
- Spear Phishing Market
Spear Phishing Market Size, Share, and Growth Forecast, 2026 - 2033
Spear Phishing Market by Component (Solutions, Services, Others), Deployment (On-premises, Cloud-based, Others), Organization Size, End-user, and Regional Analysis for 2026 - 2033
Spear Phishing Market Size and Trends Analysis
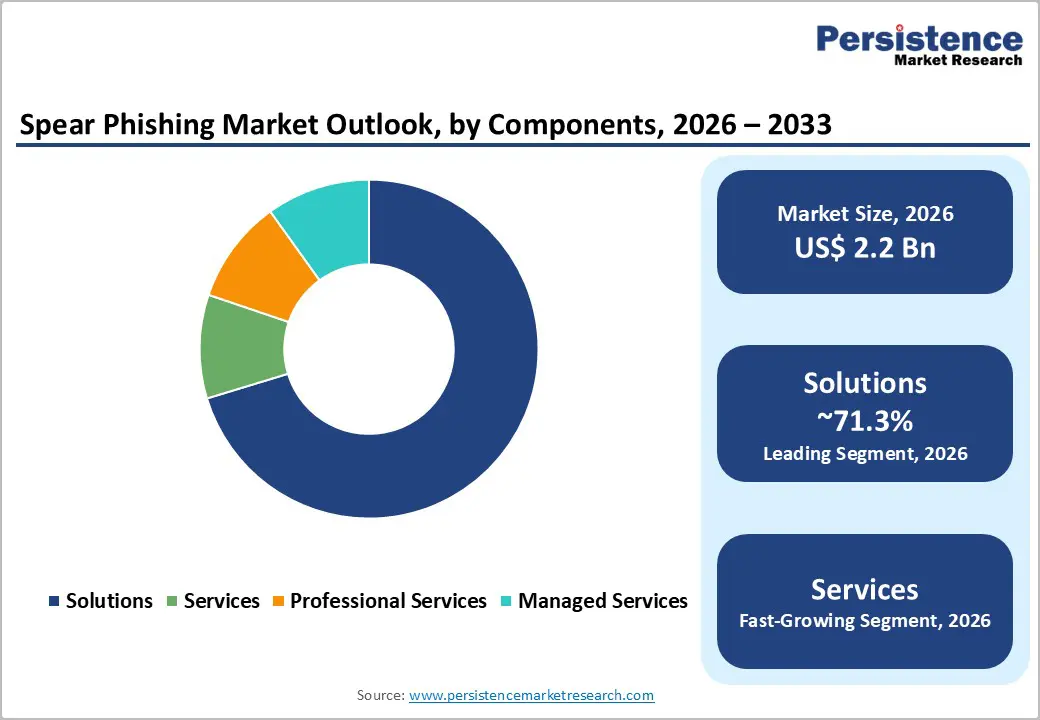
The global spear phishing market size is likely to be valued at US$2.2 billion in 2026 and is expected to reach US$4.9 billion by 2033, growing at a CAGR of 12.1% between 2026 and 2033, driven by increasing financial losses from business email compromise (BEC), rapid evolution of identity-based attack vectors, and stricter cybersecurity disclosure requirements.
Regulatory frameworks and rising enterprise risk exposure are accelerating investments in advanced threat detection, identity protection, and user awareness programs, positioning spear phishing mitigation as a critical component of enterprise cybersecurity strategies.
Key Industry Highlights:
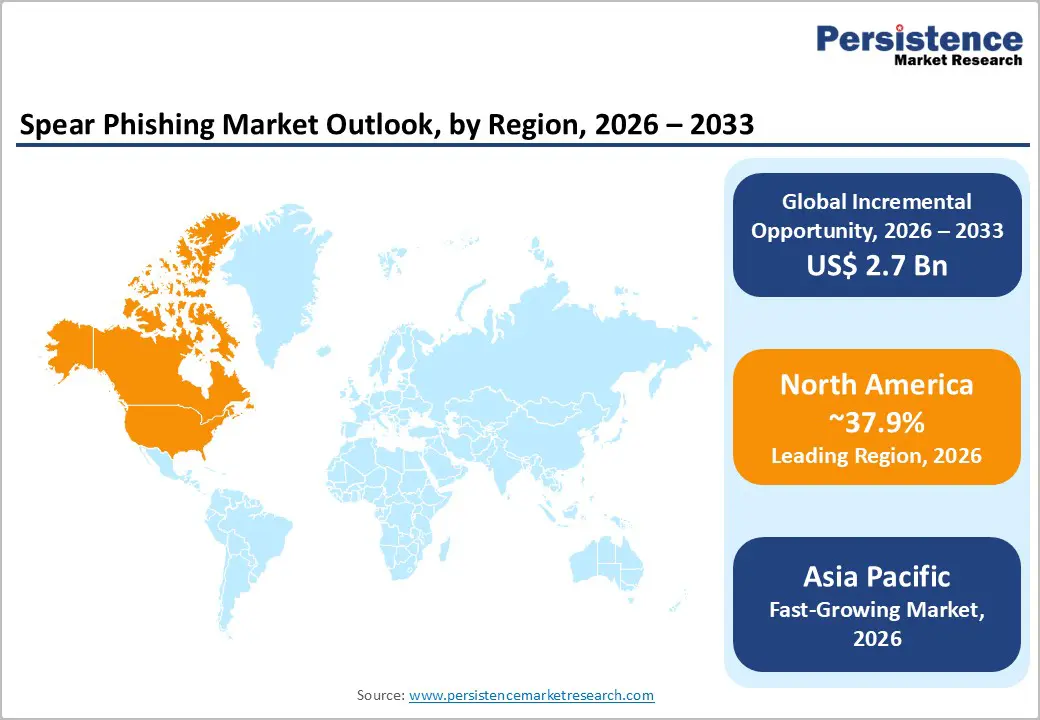
- Leading Region: North America is projected to account for 37.9% of the market share, driven by strong regulatory enforcement, high cyberattack incidence, and the presence of leading cybersecurity vendors.
- Fastest-growing Region: Asia Pacific is the fastest-growing region, fueled by rapid digital transformation, increasing cloud adoption, and rising cyber threat exposure across emerging economies.
- Investment Plans: Organizations are increasingly allocating budgets toward AI-driven threat detection, identity-centric security, and managed security services, with a strong focus on phishing-resistant authentication and zero-trust architectures to mitigate evolving attack vectors.
- Dominant Component: Solutions dominate, anticipated to account for 71.3% of the market share, driven by the increasing adoption of AI-powered email security, threat detection, and identity protection platforms
- Leading Deployment: On-premises deployment remains the dominant model, holding an anticipated share of 53.5%, as enterprises prioritize data control, regulatory compliance, and customized security infrastructure.
| Key Insights | Details |
|---|---|
| Spear Phishing Market Size (2026E) | US$2.2 Bn |
| Market Value Forecast (2033F) | US$4.9 Bn |
| Projected Growth (CAGR 2026 to 2033) | 12.1% |
| Historical Market Growth (CAGR 2020 to 2025) | 10.7% |

DRO Analysis
Driver Analysis - Escalating Business Email Compromise (BEC) Losses Driving Security Investments
The increasing financial impact of BEC attacks is a primary driver of the spear phishing market. Reported global losses from cyber-enabled fraud continue to rise significantly, with BEC incidents representing one of the most costly categories. These attacks typically originate from compromised or spoofed email accounts, making spear phishing a highly effective entry point. Organizations are responding by investing in advanced email security gateways, identity verification systems, and threat intelligence platforms. The shift toward proactive defense mechanisms reflects a growing recognition that traditional perimeter-based security is insufficient against targeted social engineering attacks.
AI-Driven Attack Sophistication Increasing Demand for Behavioral Detection
Artificial intelligence is significantly enhancing the precision and scalability of spear phishing attacks. Threat actors are leveraging AI to craft highly personalized messages, mimic communication patterns, and automate large-scale campaigns. This has led to a measurable increase in attack success rates compared to generic phishing attempts. As a result, organizations are adopting AI-powered security solutions that focus on behavioral analytics, anomaly detection, and identity telemetry. These technologies enable real-time identification of suspicious activities, reducing reliance on static signature-based detection and improving overall threat response effectiveness.
Regulatory Compliance Requirements Elevating Cybersecurity Prioritization
Evolving cybersecurity regulations are transforming spear phishing prevention into a compliance necessity rather than an optional investment. Mandatory disclosure requirements for cyber incidents and expanded regulatory frameworks across critical sectors are compelling organizations to enhance their security posture. These regulations emphasize timely incident reporting, risk management, and continuous monitoring, driving demand for integrated security solutions and managed services. The regulatory environment is particularly influential in sectors such as finance, healthcare, and critical infrastructure, where compliance failures can result in substantial financial and reputational consequences.
Restraint Analysis - Resource Constraints Limiting Adoption Among Small and Medium Enterprises
Despite growing awareness, many SMEs face significant barriers to adopting advanced spear phishing protection solutions. Limited cybersecurity budgets and a shortage of skilled professionals restrict their ability to implement comprehensive security frameworks. While cloud-based and managed services offer cost-effective alternatives, adoption remains uneven. This creates a structural challenge for market expansion, as a large portion of potential users continues to rely on basic or reactive security measures.
Operational Complexity and Alert Fatigue: Reducing Efficiency
Security operations centers (SOCs) often face high volumes of alerts, many of which require manual investigation. This leads to alert fatigue, delayed response times, and reduced operational efficiency. Fragmented security tools further complicate workflows, making it difficult to achieve centralized visibility and control. As a result, organizations may hesitate to invest in additional point solutions, preferring consolidated platforms that simplify management and improve accuracy.
Opportunity Analysis - Expansion of Identity-Centric and Browser-Level Security Solutions
The shift toward identity-based attacks has created significant opportunities for solutions that extend beyond traditional email security. Emerging technologies are increasingly focused on protecting user sessions, access tokens, and authentication workflows, which are now primary targets for attackers. Browser-level security and zero-trust architectures are gaining traction as organizations move toward securing endpoints and cloud environments holistically rather than relying solely on perimeter defenses. For example, companies such as Zscaler and Microsoft are integrating identity-aware access controls and session monitoring into their platforms. This evolution reflects a broader market shift toward continuous authentication and real-time risk assessment, positioning vendors with integrated identity protection capabilities to capture a growing share of cybersecurity budgets.
Growth of Managed Security Services and Awareness Programs
Managed services represent a substantial growth opportunity, particularly for organizations that lack internal cybersecurity expertise or face resource constraints. These services encompass 24/7 threat monitoring, incident response, phishing simulations, and employee awareness training, helping organizations build resilience against increasingly sophisticated attacks. Providers such as Cofense and CrowdStrike are expanding their managed detection and response (MDR) and phishing defense offerings to meet this demand. Continuous awareness programs are becoming critical, as human error remains one of the most exploited vulnerabilities in spear phishing campaigns. The transition toward subscription-based and service-driven models is also enhancing revenue predictability for vendors while improving long-term customer engagement and retention.
Adoption of Phishing-Resistant Authentication Mechanisms
The growing limitations of traditional multi-factor authentication (MFA), particularly its vulnerability to social engineering and token interception, are accelerating the adoption of phishing-resistant alternatives. Technologies such as passwordless authentication, FIDO2-based security keys, and biometric verification are gaining widespread acceptance as more secure identity validation methods. Companies such as Cisco Systems and CrowdStrike are actively developing solutions that emphasize strong identity assurance and eliminate reliance on easily compromised credentials. As organizations modernize their identity infrastructure and adopt zero-trust frameworks, demand for these advanced authentication mechanisms is expected to increase, creating new growth avenues across both enterprise and SME segments.
Category-wise Analysis
Component Insights
Solutions dominate the market and are anticipated to account for 71.3% of the market share in 2026. This dominance reflects strong demand for integrated platforms that combine email security, threat detection, and identity protection into a unified architecture. Organizations increasingly prioritize solutions capable of identifying malicious URLs, detecting domain spoofing, and flagging abnormal communication patterns in real time. For instance, platforms such as Microsoft Defender for Office 365 and Proofpoint Targeted Attack Protection are widely deployed to mitigate executive impersonation and BEC attacks. The effectiveness of these tools in reducing financial fraud, credential theft, and lateral movement risks has reinforced their position as a core layer in enterprise cybersecurity frameworks.
Services are the fastest-growing segment due to increasing reliance on external expertise. Organizations are increasingly turning to managed security services, consulting, and training programs to address skill shortages and operational complexity. These services include phishing simulation campaigns, incident response, and continuous threat monitoring. Providers such as Cofense offer phishing detection and response platforms integrated with employee reporting workflows, while managed detection and response (MDR) services from firms such as CrowdStrike enable real-time threat containment. The growing sophistication of attacks and regulatory compliance requirements is accelerating adoption, particularly among SMEs and highly regulated sectors such as BFSI and healthcare.
Deployment Insights
On-premises deployment is expected to lead the market, holding a 53.5% share in 2026. This model remains preferred among organizations requiring strict data governance, regulatory compliance, and internal control over security infrastructure. On-premises solutions enable customized policy enforcement, deeper integration with legacy systems, and enhanced visibility into internal communications. Industries such as banking and government often rely on vendors like Broadcom (Symantec enterprise security) and Trend Micro for on-premise email and threat protection deployments. Despite higher upfront costs and maintenance requirements, these solutions offer the level of control and data residency assurance that large enterprises and regulated entities demand.
Cloud-based deployment is expected to be the fastest-growing segment, supported by scalability and operational flexibility. Cloud-native security solutions allow organizations to deploy protections rapidly, scale resources dynamically, and integrate seamlessly with SaaS platforms and remote work environments. Solutions such as Zscaler and Mimecast enable real-time threat detection across distributed networks and cloud applications. The shift toward hybrid work models and multi-cloud architectures is further accelerating adoption. Hybrid deployment models are also gaining traction, enabling organizations to combine the control of on-premises systems with the agility and advanced analytics of cloud platforms, optimizing both performance and cost efficiency.
Regional Insights
North America Spear Phishing Market Trends
North America is projected to lead the market, holding a 37.9% share in 2026, with the U.S. acting as the primary growth engine. The region’s dominance is supported by a high incidence of targeted cyberattacks, widespread adoption of cloud-based enterprise applications, and a mature cybersecurity ecosystem. Organizations across sectors such as BFSI, healthcare, and technology are prioritizing investments in advanced threat detection and identity protection to mitigate financial and reputational risks. The strong presence of leading cybersecurity vendors such as Microsoft, Cisco Systems, and Proofpoint further strengthens regional capabilities by driving continuous innovation in AI-based email security and zero-trust frameworks.
Regulatory frameworks and government initiatives play a central role in shaping market behavior. Mandatory cyber incident disclosure requirements and federal cybersecurity guidelines are pushing enterprises toward proactive threat monitoring and rapid response capabilities. For example, Microsoft has expanded its Security Copilot and automated phishing triage capabilities to reduce response times and improve SOC efficiency, directly addressing alert fatigue challenges in large enterprises. Cisco Systems also introduced enhanced identity and access management solutions to counter identity-based phishing attacks. These developments reflect a broader regional shift toward AI-driven, identity-centric security architectures, reinforcing North America’s leadership through continuous innovation and high cybersecurity spending.
Europe Spear Phishing Market Trends
Europe represents a significant share of the global spear phishing market, driven by strong regulatory enforcement and increasing enterprise awareness of cyber risks. Key countries, including Germany, the U.K., France, and Spain, are at the forefront of adoption, supported by advanced digital economies and strict data protection standards. Organizations in the region are prioritizing investments in email security, identity governance, and compliance-driven cybersecurity frameworks to align with evolving regulatory requirements.
The regulatory environment emphasizes risk management, incident reporting, and data protection, which is accelerating demand for integrated security solutions. For instance, Mimecast, headquartered in the U.K., continues to expand its cloud-based email security offerings across Europe, helping organizations strengthen defenses against impersonation and BEC attacks. Similarly, Check Point Software Technologies has enhanced its email and collaboration security platforms to address sophisticated phishing campaigns targeting European enterprises. Cross-border collaboration initiatives and threat intelligence sharing are further improving regional resilience. These developments highlight how regulation-driven demand and vendor innovation are shaping a highly structured and compliance-focused market landscape in Europe.
Asia Pacific Spear Phishing Market Trends
Asia Pacific is expected to be the fastest-growing region, supported by rapid digital transformation, increasing internet penetration, and rising exposure to cyber threats. Major economies such as China, Japan, India, and Southeast Asian countries are witnessing strong growth in cybersecurity investments as organizations expand their digital operations. The increasing adoption of cloud computing, e-commerce, and digital banking is significantly enlarging the attack surface, making spear phishing a critical concern for enterprises across the region.
The region presents substantial opportunities for vendors offering scalable and cost-effective solutions. Companies such as Trend Micro, headquartered in Japan, are actively enhancing AI-driven threat detection capabilities to address region-specific phishing threats. In India and Southeast Asia, cloud security providers such as Zscaler are expanding their presence by offering zero-trust architectures tailored to distributed workforces. CrowdStrike has also strengthened its regional operations by delivering identity protection and threat intelligence services to enterprises facing increasingly sophisticated phishing campaigns.
Despite strong growth, the region faces challenges due to varying levels of cybersecurity maturity and regulatory inconsistency across countries. However, ongoing investments in digital infrastructure, government-led cybersecurity initiatives, and workforce training programs are expected to drive sustained adoption. The combination of rapid digitization, expanding threat landscape, and increasing vendor presence positions Asia Pacific as a key growth frontier for spear phishing market.
Competitive Landscape
The global spear phishing market is moderately concentrated, with a mix of large technology providers and specialized security vendors. Leading players focus on integrated platforms that combine email security, identity protection, and threat intelligence. While major companies dominate enterprise segments, smaller vendors compete by offering niche solutions and innovative technologies.
Key strategies include AI-driven innovation, identity-centric security, cloud adoption, and managed service expansion. Companies are focusing on integrated platforms, automation, and user-centric security models to differentiate their offerings and address evolving threat landscapes.
Key Industry Developments
- In March 2025, Proofpoint announced an expanded global strategic alliance with Microsoft to build its human-centric cybersecurity platform on Microsoft Azure, enabling scalable AI-powered threat detection and enhanced protection against phishing and social engineering attacks.
- In September 2025, Proofpoint introduced multiple innovations to secure the “agentic workspace,” including AI-driven protections against prompt injection and phishing attacks targeting AI assistants, aiming to address emerging risks from AI-enabled spear phishing campaigns.
- In February 2025, CrowdStrike released its Global Threat Report, highlighting the rapid rise of AI-powered social engineering and spear phishing techniques, reinforcing the need for integrated identity, cloud, and endpoint protection platforms to counter evolving threats.
Companies Covered in Spear Phishing Market
- Microsoft
- Cisco Systems
- Proofpoint
- Broadcom
- Trend Micro
- Mimecast
- Barracuda Networks
- Fortinet
- Check Point Software Technologies
- CrowdStrike
- Zscaler
- Abnormal Security
- Cofense
- OpenText
- IRONSCALES
- GreatHorn
Frequently Asked Questions
The spear phishing market size is estimated to be US$2.2 billion in 2026.
The spear phishing market is projected to reach US$4.9 billion by 2033.
Key trends include the rise of AI-driven phishing attacks, increasing adoption of identity-centric security solutions, growing demand for managed security services, and the shift toward zero-trust and phishing-resistant authentication frameworks.
The solutions segment is the leading component category, accounting for the largest share of 71.3%, driven by demand for integrated email security and threat detection platforms.
The spear phishing market is expected to grow at a CAGR of 12.1% from 2026 to 2033.
Some of the companies include Microsoft, Cisco Systems, Proofpoint, CrowdStrike, and Trend Micro.







